
 In any effective risk management program, you will find a team of dedicated analysts armed with robust analyses. However, an analysis is only as effective as the rationale. I have identified five simple components that help in any risk assessment, with the FAIR model or other methods.
In any effective risk management program, you will find a team of dedicated analysts armed with robust analyses. However, an analysis is only as effective as the rationale. I have identified five simple components that help in any risk assessment, with the FAIR model or other methods.
While I touch on them briefly, I tie them all together in the examples at the end.
1. Specific Examples
Most organizations do not have as much visibility as they would like and in fact most Subject Matter Experts (SMEs) would argue for their inability to find data that is vital to your analysis. This is where using specific examples allow for data to come to light and the analysis as a whole to be more robust and defensible. Using real life pain points or scenarios in your rationale gives a reference for the reader.
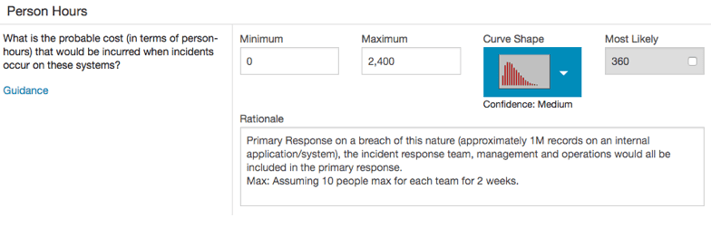
These specific examples can be used to justify Minimum, Maximum and Most Likely in any aspect of the analysis. I generally use a simple breakdown within my risk assessment rationale. If this is a broad analysis, I use different examples for each aspect of my range. If this is a specific analysis, I use one topic example, with the various outcomes we have seen.
Examples:
Min: 0, availability outage of internal payment system has not occurred due to outdated technology.
Max: 50, availability outage of internal application for warehouse management and sorting facilities occurred last year alone.
M/L: Reflects Min, as most situations have transpired accordingly.
2. Simplicity
Using details in the scenario aids in defending your range of data points. The details on the scenario, controls, and generally “why”, must be accomplished in the most effective manner. If you can get the message across in 50 words or 500 – choose effectively.
While details do matter, trust that the organization’s history or the scenarios you chose to reference are relatively known. Only include relevant details.
Example:
Time is associated with an IT associate re-imaging the laptop as well as a security personnel recording the event within IR.
3. History Matters
We are NOT forecasting an organization’s loss. I am not a fortune teller. I do not have a crystal ball. What I do know is that we can conduct effective analyses to make business decisions based on historical data. I would not conduct an analysis that builds in any sort of prediction. I do not pretend to know what will change over time; what I do know is what I see and that is the strongest tool in my belt.
4. Disclose Your Confidence
If you cannot find data, don’t have Subject Matter Experts, or simply are not confident in your ranges, explain why. I have never been faulted for being upfront in this manner. I believe analysis of any sort contains many variables and factors that could change the analysis completely. This is why I state my confidence in my analysis and speak to that in the rationale.
Example:
The estimates represent an estimation of resistance strength if ransomware were to land within a user’s inbox. The two key controls are A/V signature-based identification (effective against only known ransomware) as well as user training where they would self-identify and not attempt to install the software (testing shows only 30% effectiveness). Based on data provided, selected low confidence to use the entire range.
5. Know the Important Factors
When conducting an analysis that addresses an initiative or a change over time, identify the control or factor at play and disclose this. Use this in your report and rationale – it will show how well thought-out the analysis is.
How Everything Ties Together
In your rationale, you want to speak to all data points gathered and all factors within the analysis. Most robust rationale form some sort of language such as the following:
Based on historical data, it is not common that ransomware that infects a user’s workstation would then spread to a mapped drive(s). This is because most users do not have automatically mapped drives.
Related:
What Makes a Good Risk Analyst?









