In today’s risk-saturated environment, organizations are under increasing pressure to demonstrate the effectiveness of technology and cybersecurity controls not just to regulators and auditors, but to their own boards and stakeholders.
Yet too often, control frameworks are either too generic to be meaningful or too rigid to adapt to the nuances of a specific business. It is common for stakeholders to feel like technology controls are too vague or that the goal post is always changing.
To address these challenges, organizations must rethink how risks and controls are designed by establishing a common control framework that is customized to the organization and tightly linked to its top risks.
 Author Daniel Stone is a Director in Protiviti's Security & Privacy practice. Join Daniel for a webinar “Enhancing Security Frameworks with FAIR: A Practical Integration Guide, on September 4 at 1:00 pm ET.” Register here.
Author Daniel Stone is a Director in Protiviti's Security & Privacy practice. Join Daniel for a webinar “Enhancing Security Frameworks with FAIR: A Practical Integration Guide, on September 4 at 1:00 pm ET.” Register here.
Why “common” doesn’t mean “one-size-fits-all”
The term “common control framework” often gets misinterpreted. It doesn’t mean a universal set of controls that every organization should blindly adopt. Instead, it refers to a shared language and structure that can be tailored to reflect the organization’s operating model, regulatory exposure and risk appetite.
We’ve seen the value of starting with a baseline framework—whether it’s the NIST Cybersecurity Framework or NIST SP 800-53 Rev. 5, ISO 27001, or a sector specific framework—and then mapping those controls to the organization’s actual risk landscape. Once mapped, these controls can be combined or split out based on the level of detail and guidance that is needed for your environment. This mapping isn’t just a compliance exercise. It’s a strategic alignment that ensures controls are not only present but purposeful.
Linking controls to risk scenarios: The missing piece
A control framework without a risk scenario taxonomy is like assembling furniture without instructions. You might have all the pieces, but without context and an understanding of the full picture, it’s nearly impossible to ensure everything fits together as intended.
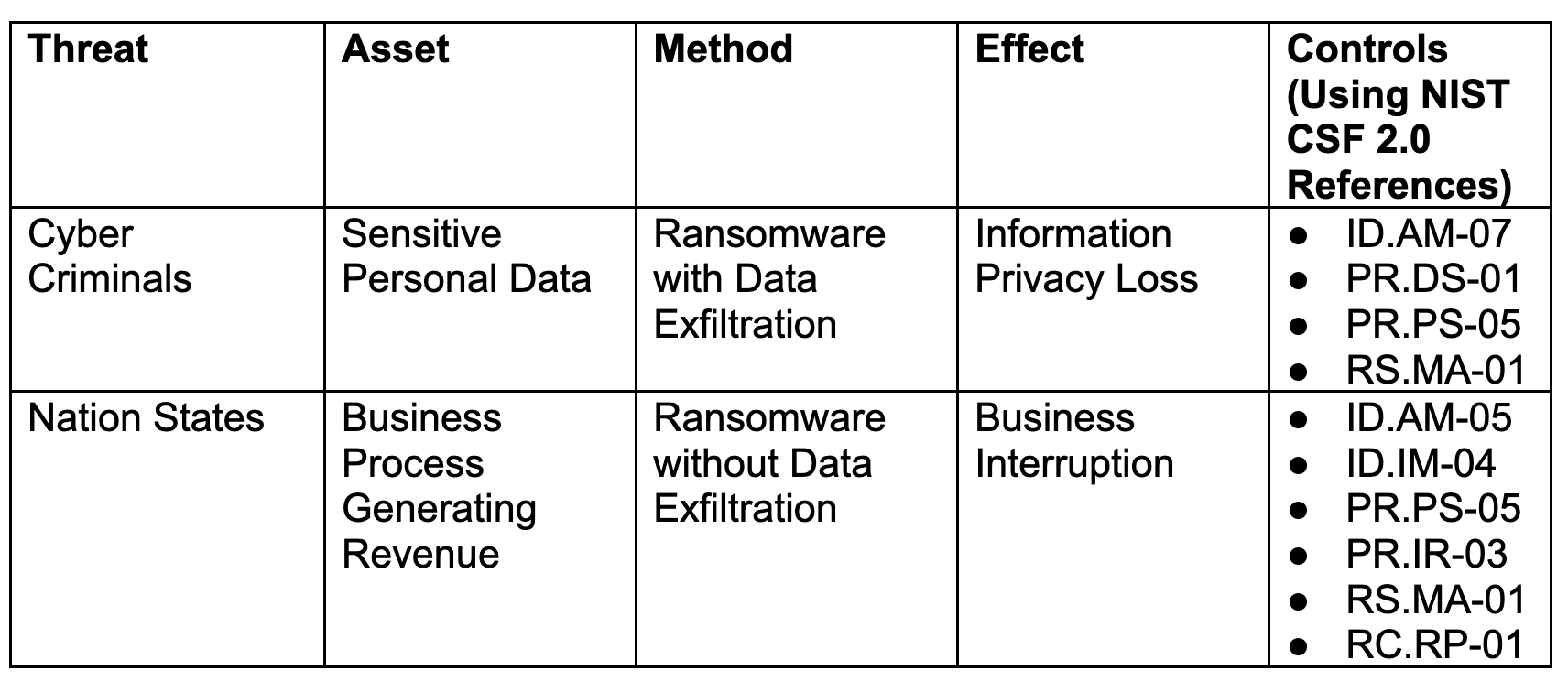
That’s why Protiviti has been emphasizing the importance of defining a risk taxonomy as a precursor to control design. Using the FAIR Institute’s cyber risk taxonomy, for example as outlined in the below table, Protiviti helps clients define which of these scenarios apply to them and customize risk scenarios based on threat actor, asset, method and effect. These scenarios become the lens through which control relevance is evaluated.
Other starting frameworks exist, but the importance of customizing the framework to your organization’s key risks and assets of business value cannot be overstated. The only thing worse than having no risk taxonomy is having a library of 200 risks that aren’t important or relevant to your business.
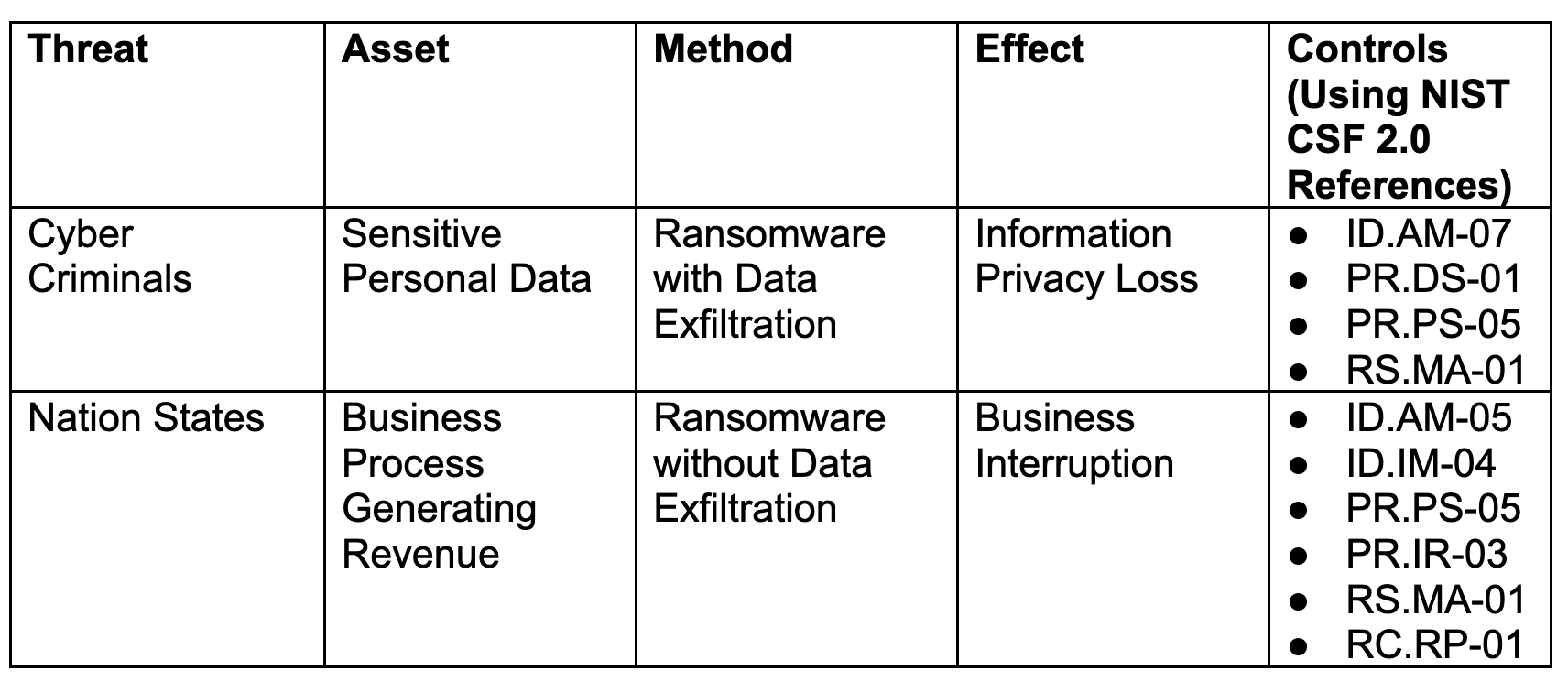
Vague or poorly measured risk scenarios can lead to misaligned controls and wasted resources. By contrast, clearly defined scenarios allow for risk-based control application, and the ability to ensure controls are tiered based on business criticality and regulatory or compliance exposure.
Tiering and instantiation: Making controls actionable
One of the most powerful concepts Protiviti has implemented is differentiating between control expectations and the model by which those controls are implemented in practice at the product, asset or business unit level. This approach allows organizations to maintain a centralized control library while tailoring control procedures to specific contexts.
The evolution of governance, risk and compliance (GRC) tools and processes have enabled significant improvements in overall governance maturity. These tools today more effectively enable control owners to understand exactly what’s expected of them than ever before, and in turn there is a clearer path for organizations to demonstrate technology compliance.
Metrics that matter
When controls are linked to risk scenarios, measurement becomes meaningful. Instead of tracking control coverage in isolation, we can assess risk reduction in dollar terms, forecast losses and prioritize remediation based on impact.
In one example, Protiviti replaced five legacy controls with a single, well-defined control that covered all necessary elements and tied directly to the risk scenarios that this control mitigated. The result? Reduced testing effort, clearer accountability and better alignment with the organization’s risk appetite.
A practical approach: From risk to controls in six steps
To make this real, here’s a simplified roadmap we’ve used to help organizations build a risk-aligned control framework:
- Identify key risks and business-critical assets
Start with what matters most (i.e., your crown jewels) and define the top risks that could impact them. - Understand the top threats
Map out threat actors, attack vectors and potential impacts to validate your risk scenarios and understand what is most likely to impact your environment. - Select a baseline framework
Choose a foundational model like the NIST CSF, or combine control objectives that are relevant to you from meta-frameworks such as the Secure Controls Framework (SCF) or the Unified Compliance Framework (UCF), that fit your regulatory and operational context. - Map controls to risk scenarios
Align each control to the risks it mitigates, tier them by criticality and contextualize them by business unit or asset. - Define a control taxonomy
Establish a clear structure for control types, categories and ownership to support governance and reporting. - Operationalize in a GRC tool
Enable the framework in your GRC platform to automate workflows, evidence collection and continuous improvement.
A living framework
It’s critical to treat the control framework as a living document. Risks evolve. Regulations change. Business models pivot. Your framework should be flexible enough to adapt without losing its integrity.
Establishing formal intake processes for each of the following must be integral to your initial program:
- Changes to control regulations or mappings (which can be enabled effectively by a GRC tool)
- Clear issues and exceptions tracking and approval processes
- Continuous improvement cycles, and governance structures that incorporate lessons learned from audits, incidents, and regulatory reviews
This makes the framework continually relevant and resilient and helps ensure continued value from the approach. A common control framework isn’t about standardization for its own sake. It’s about creating a structured, adaptable foundation that reflects each organization’s unique risk profile. By linking controls to well-defined risk scenarios, tiering them appropriately and validating implementation of them where they matter most, it is possible to build a framework that not only satisfies compliance, but drives real risk reduction.
Want to see how the FAIR model can be practically integrated into your security framework? Don’t miss Protiviti’s upcoming webinar, Enhancing Security Frameworks with FAIR: A Practical Integration Guide, on September 4 at 1:00 pm ET. Learn actionable strategies from our experts and get your questions answered in real time. Register here.




.jpeg)
.png)
.png)


