FAIRCON2020 Video: How Cimpress Prioritizes NIST CSF Activities with FAIR and the MITRE ATT&CK Framework
 You’re probably using the NIST CSF, the most popular cybersecurity framework, as a checklist of best practices but it could do a lot more for your organization. In fact, combining the framework with the FAIR standard could be the starting point for aligning risk management, security and the business to reach a goal that’s a struggle for many organizations: proving the business value of a cybersecurity program.
You’re probably using the NIST CSF, the most popular cybersecurity framework, as a checklist of best practices but it could do a lot more for your organization. In fact, combining the framework with the FAIR standard could be the starting point for aligning risk management, security and the business to reach a goal that’s a struggle for many organizations: proving the business value of a cybersecurity program.
That was the message from Richard Barretto, Manager of Security Operations for Cimpress, the multinational company best known in the US for its Vistaprint brand, in his presentation at the recent 2020 FAIR Conference.
Watch the video: Prioritizing NIST CSF Activities with FAIR on the FAIR Institute LINK member resources site. A membership is required for access – join the FAIR Institute now.
Learn more: NIST CSF and FAIR Integration at Cimpress Called “Success Story” by NIST
Barretto, who manages both the SOC and GRC for Cimpress, shared the roadmap Cimpress has followed for CSF/FAIR integration:
Catalogue the top risks to the business
Barretto’s team interviewed the leaders of each of the 15 business units to learn what they saw as top risks. Mostly, those were operational risks, which the team converted to cyber risk scenarios and quantified them using FAIR. With those financial values, they also established risk tolerance. The business leaders saw that as an immediate value.
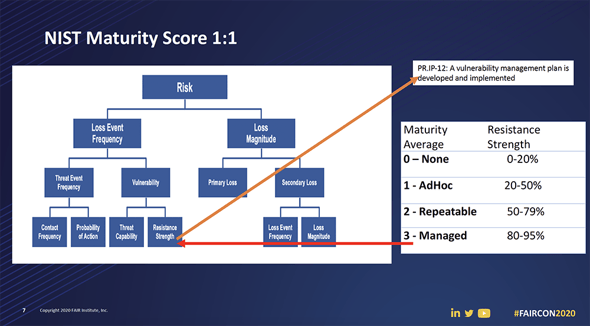
Map NIST controls to top risk scenarios
Some challenging questions here in identifying appropriate controls:
- How to support a scalable rationale for resistance strength in FAIR risk analyses
- What controls would give the best value
- How to find transparency between risk and controls
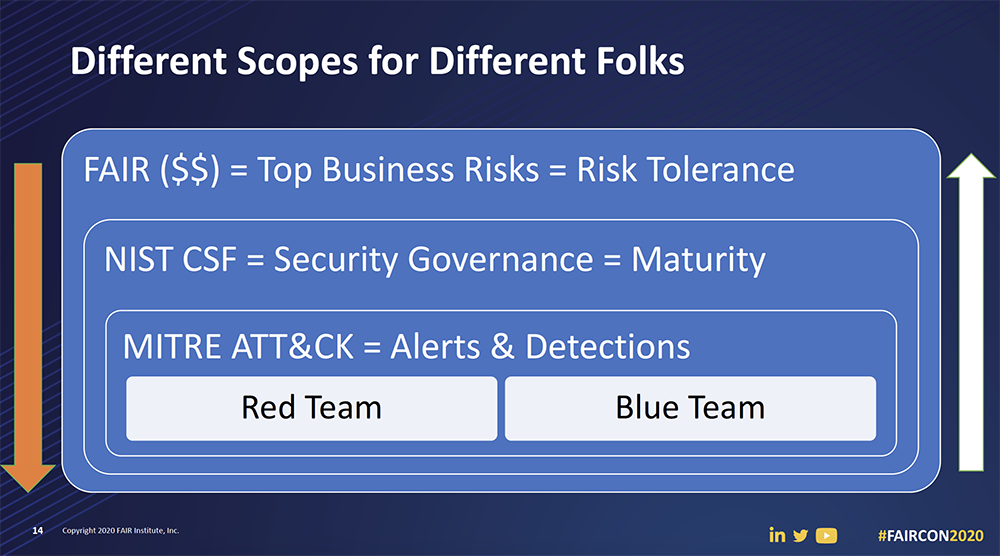
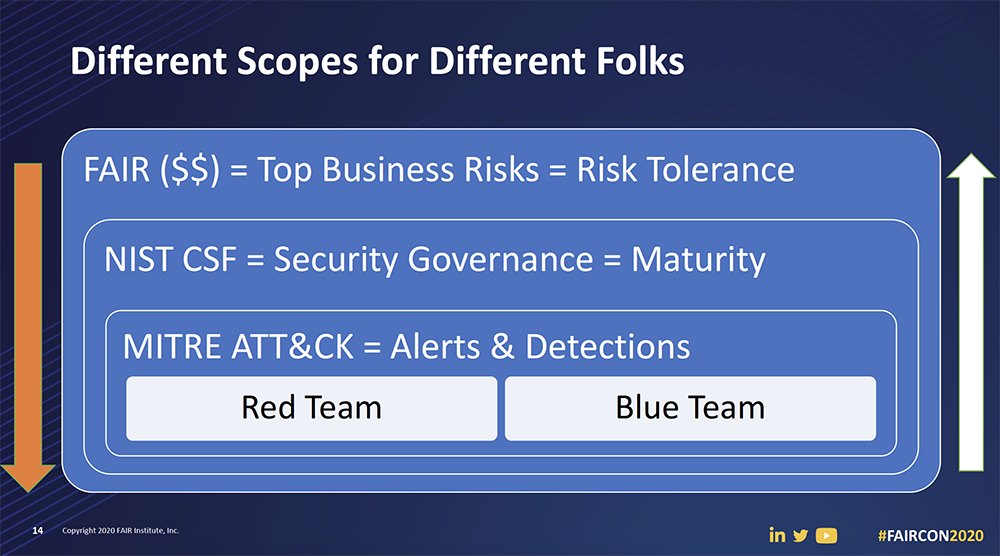
Combine MITRE ATT&CK and FAIR
They used RiskLens simulations to identify weak spots and blind spots (“a humbling experience,” Barretto said). That showed where they needed to improve controls or alert and detection. They used the MITRE ATT&CK framework to plot out likely vectors of attack against their weaknesses in loss event scenarios for the Cimpress top risks.
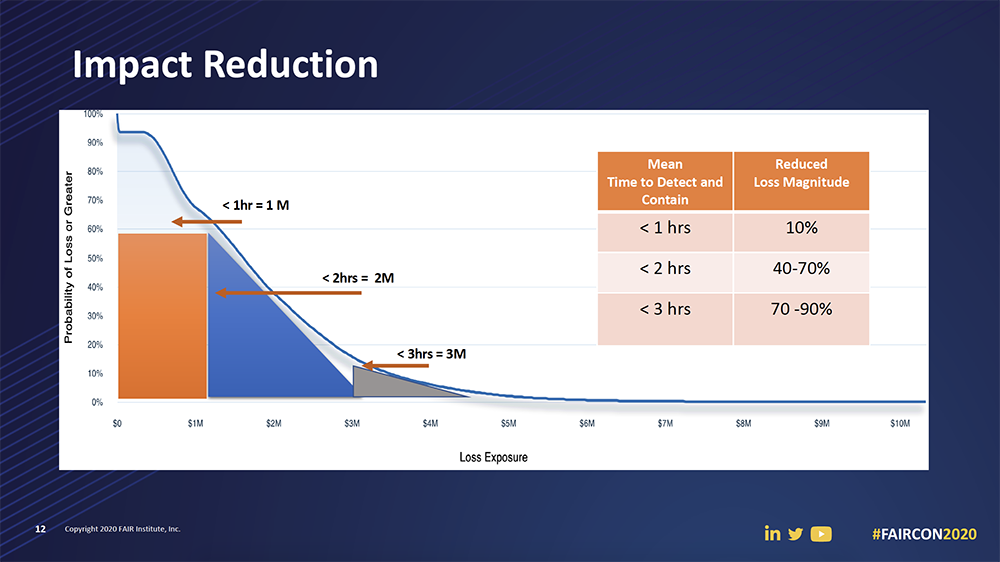
Quantify SOC performance in reduced loss magnitude
Barretto’s team realized that tracking mean time to alert and mean time to detect could be SOC performance metrics that could be tied back to FAIR via loss magnitude, solving a perennial SOC problem of many incoming alerts with no way to know the business impact of any. That’s still a work in progress but the results look like this:
Tie it all together
As Barretto sums it up:
“From a top level down you have your controls that map to your top risks, so we know that set of controls that we have to focus on, but now we also have the alerts and detections that we also need to elevate or escalate because they are already tied back to the top risks.
“Now we have [probable loss in] dollars so If we ever have to ask management for investments, we can easily tie back the controls to detections, back to those top risks.
“Melding these three frameworks…gave us an end-to-end picture of our security program from the very low level of an attack or even configurations all the way to the top.”
Watch the video: Prioritizing NIST CSF Activities with FAIR on the FAIR Institute LINK member resources site. A membership is required for access – join the FAIR Institute now.
Related:
FAIRCON2020 Video: How Highmark Health Combines FAIR and HITRUST for Better Cyber Risk Management
NIST Maps FAIR to the CSF - Big Step Forward in Acceptance of Cyber Risk Quantification









