FAIRCON23 Day 2: SEC Talks Cyber Disclosure, Jack Jones Talks Risk 2.0

 As dawn broke over the Fairmont Hotel in Washington, DC, on Wednesday, October 18, it was hard to imagine that the 2023 FAIR Conference Day Two could match Day One for intensity and engagement (see FAIRCON23 Day One).
As dawn broke over the Fairmont Hotel in Washington, DC, on Wednesday, October 18, it was hard to imagine that the 2023 FAIR Conference Day Two could match Day One for intensity and engagement (see FAIRCON23 Day One).
But the day’s agenda kept up the pace, with a keynote by FAIR creator Jack Jones on a new way of thinking about risk management, an appearance by David Hirsch of the SEC, the man of the hour in the risk regulatory world, and a lineup that had one speaker say he wished he could clone himself so he could simultaneously attend other sessions.
Cyber Risk Management Prescription from Jack Jones
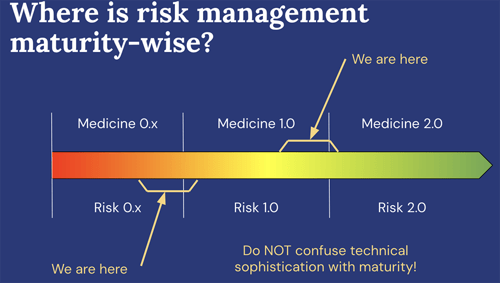
“Let’s talk medicine,” Jack surprisingly began his keynote on "The Future of Risk Analysis in an AI and Automation World". Jack explained that medicine is moving from the epoch of Medicine 1.0 – scientific but only reactive to disease – to Medicine 2.0 – proactively focused on living longer and healthier by understanding root causes in genetics, environment, and lifestyle.
Jack argued that risk management is stil mostly in its reactive epoch 1.0. He envisioned a proactive epoch 2.0 based on science, the “controls physiology” behind the FAIR Controls Analytics Model (FAIR-CAM™), with root cause analysis powered by AI.
The Voice of Authority on New SEC Disclosure Rules
FAIRCON23 rolled right into the next session, a keynote discussion on “How to Get Ready for the New SEC Rule on Cybersecurity,” particularly the requirement to disclose a cyber incident of material impact within four days of determining the damage had crossed into materiality.
The discussion was moderated by The Wall Street Journal cybersecurity editor Kim Nash, with panelists Brian Walker, CEO, The CAP Group, Kurt John, Chief Security Officer, Expedia Group, Richard Borden, Cybersecurity and Privacy Partner, Frankfurt, Kurnit, Klein, & Selz – but all eyes were on David Hirsch, Chief of the Crypto Asset and Cyber Unit, Division of Enforcement, SEC.
So, let’s jump to his key points:
Right: Kim Nash and David Hirsch
 >>The SEC tightened its rules because it was clear from cyber loss events in the news that companies were under-reporting to the agency (by 8-K forms).
>>The SEC tightened its rules because it was clear from cyber loss events in the news that companies were under-reporting to the agency (by 8-K forms).
>>”I don’t think there is an expectation on the part of regulators that anyone is going to have perfect visibility and a perfect explanation of what occurred ...within 4 days. It’s contemplated that it’s an iterative process.”
>>He urged companies to keep good logs and records so “we can see the decisions made were based on the best available information, they were reasonable and within the bounds of expected conduct.”
>>Although the SEC dropped a proposed rule that boards disclose their expertise in cybersecurity, companies should still look at such a disclosure as “not so much a burden as an opportunity to extol the virtues of what you’ve already been doing.”
Material Risk in Cyber? Cue FAIR-MAM
At FAIRCON, the FAIR Institute held its first public meeting on the FAIR Materiality Assessment Model (FAIR-MAM™), led by the model’s creator, Erica Eager, with approving reviews from a regulator, Filippo Curti, Federal Reserve of Richmond, and a practitioner, Tom Macphee of Cigna.
Read more about FAIR MAM and don’t miss the materiality calculator powered by this model (and introduced at the Conference Monday), “How Material Is that Hack? HowMaterialIsThatHack.org.
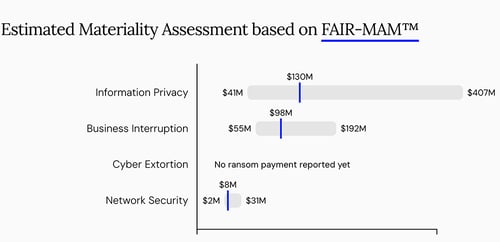
Report from How Material Is that Hack? website
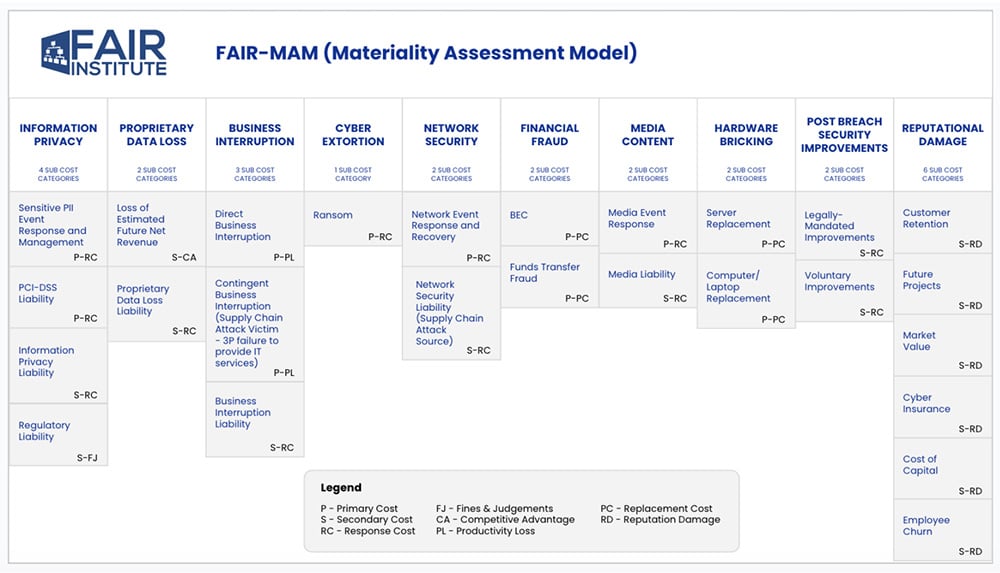
FAIR-MAM Detail
SEC Rules: Board Members Weigh In
“How is the Discussion About Cyber Risk Changing at the Board Level?” this session asked and…did we mention the new SEC rules? Kris Lovejoy, a rare combination of board member (Dominion Energy) and a senior cybersecurity practitioner (Kyndryl) put the issue in perspective:
“Our job interpreting the new SEC guidance, is have to have an effective, mature cybersecurity program in place” not get hung up on defining materiality. The key elements of an effective program would be a governance and management process, an established risk tolerance, a risk management framework, and reportable metrics. “It’s a material incident if all of those fail.” Elias Oxendine IV, CISO, Yum! Brands had a straightforward response to the confusion introduced by the SEC: Hire a chief risk officer (CRO) to own the problem across silos.
An Explosion in FAIR-based Creativity across Risk Management
On full display a FAIRCON23: The remarkable outgrowth from the basic FAIR standard to meet the challenges of AI and other fast-moving changes to the risk landscape. Look at these sessions advancing techniques mostly new since the last FAIR Conference:
>>“Accelerating Your GenAI Adoption through AI Risk Posture Management”
Brandon Sloane from Meta and Pankaj Goyal, Research Director at the FAIR Institute, showed how standard risk scenario creation could be applied to the novel situations brought on by artificial intelligence. They also introduced a new open-community website presented by Safe Security at Genairisk.ai, “a comprehensive GenAI Risk Posture Management Platform to help you make decisions on GenAI.” It includes libraries of risk scenarios and controls.

Left to right Vidit Baxi, Jon Baker and Arvin Bansal
>>”Modeling Ransomware Risk Using FAIR and ATT&CK”
Presented by Jon Baker, Co-founder and Director, Center for Threat-Informed Defense, Vidit Baxi, CISO, Safe Security and Arvin Bansal, CISO, Nissan Motor Corp. with the goal to “leverage ATT&CK and real data in the FAIR Model” to better understand the FAIR factors of Resistance Strength, Probability of Action, and Threat Capability.
>>”Quantifying Multi-Product Security and Privacy AI Risk with FAIR and NIST AI RMF”
Tyler Britton, Security Engineer, Dropbox and Taylor Maze, Risk & Governance Manager, Dropbox used FAIR practices to poke into a modern-day problem: the harm (if any) of “hallucinations” created by AI. “How you develop/deploy AI, and what you use it for determines its risk,” they conclude.
>> Measuring Controls Effectiveness and Risk with FAIR-CAM™ - Tyler Britten, Dropbox ,and Bryan Smith, Safe Security, dig into the tricky problem of finding good data for control efficacy to feed the new FAIR Controls Analytics Model.
>>Patch Prioritization with FAIR-CAM. Denny Wan, Chair of the FAIR Institute FAIR-CAM workgroup, John Linford, Forum Director, The Open Group, and Sasha Romanosky, Senior Policy Researcher, RAND, paired FAIR-CAM with EPSS, a data-driven model for estimating the probability that a vulnerability will be exploited in the wild in the next 30 days.
Concluding Words from Jack Jones and Nick Sanna
In parting remarks, Jack Jones expressed his “gratitude and amazement for the participation of folks like you….It takes a village to raise a profession…22 years ago when I started to develop FAIR, I had no grand vision of something like this.
“The other thing too is, this year feels different. I’m not sure I can put my finger on it but it's definitely there. There are pieces of evidence: The quality of the people on the stage and the topics being discussed.”
Nick agreed: “This year, something really is happening. We used to have discussions among ourselves that cyber risk is business risk, but what can we do to convince our higher-ups?” This year, on stage the conference heard from board members, lawyers, the chief enforcer at the SEC, a Federal Reserve regulator, all saying yes, cyber risk is business risk.”
“What we are doing here is being recognized more and more as the best practice in the industry.”

Big shout-out to conference organizer Luke Bader.
This isn’t the end! Join the FAIR Institute as a Contributing Member, gain access to videos on demand covering the FAIRCON 23 sessions.




.png)




