FAQ’s about Cyber Risk Disclosure Answered by SEC Cyber Enforcement Chief Kristina Littman at FAIRCON2020 (Video)

 The U.S. Securities and Exchange Commission keeps raising the bar for public companies on what it expects for disclosure of cyber risk, with guidance that makes it clear that material cyber risks must be reported with the same transparency and in the same financial terms as is standard for other business risks—and that boards and senior executives will be held accountable for governance of cybersecurity risk management. The SEC has backed up its guidance with enforcement actions against Yahoo! and Facebook for disclosure violations.
The U.S. Securities and Exchange Commission keeps raising the bar for public companies on what it expects for disclosure of cyber risk, with guidance that makes it clear that material cyber risks must be reported with the same transparency and in the same financial terms as is standard for other business risks—and that boards and senior executives will be held accountable for governance of cybersecurity risk management. The SEC has backed up its guidance with enforcement actions against Yahoo! and Facebook for disclosure violations.
So, this was a closely watched session at the recent 2020 FAIR Conference: “Clarifying the SEC’s Expectations for Cyber Risk Disclosures”, an interview with Kristy Littman, Chief, Cyber Unit, Division of Enforcement of the SEC, by Randy Sabett, Special Counsel and Cyber Expert at Cooley LLP. You can watch the video of the session at the FAIR Institute’s LINK community site (Institute membership required).
Littman gave guidance on disclosure reporting that lines up closely with the FAIR approach to risk:
- Report on the “full range of harm” that could result from primary and secondary risk exposure
- Measure your cyber risk – “willful blindness” is not a smart regulatory strategy
- Be prepared to defend your disclosure for fullness and completeness – as quantified analysis enables
- Technology and disclosure compliance teams need to be in synch on risk – FAIR provides the common financial language
The interview covered many of the frequently asked questions from cybersecurity risk management professionals. Here are some excerpts of Littman’s answers – watch the video of the session to catch the details.
What constitutes a material event that must be disclosed?
“The first bucket of considerations is the nature and extent and potential magnitude of the incident, particularly as it relates to the importance of any compromised information…
“The other piece of the nature and extent of the incident is how it’s going to impact your company’s operations…
“Then you need to think about the range of harm that you could experience from the incident. It could be reputational, it could impact your financial performance, particularly if it is going to impact customer or vendor relationships…or if there is litigation or regulatory consequences…'
Some argue that it’s better to not quantify risk in financial terms, that ignorance might protect the company legally.
“Willful blindness is never a good strategy from a legal perspective.
"(Securities) issuers are also responsible for maintaining effective disclosure controls and procedures…You want those controls to enable the company to identify security risks and incidents to think about the significance of the impact on the business.
“It’s pretty important from a governance perspective to have open communication between the technology folks who can make those risk assessments and the disclosure folks who have to make those determinations…not just about incidents but also the risks that the company faces.”
Here is some typical language from a 10-K on risk factors. Is this the kind of disclosure you want to see?
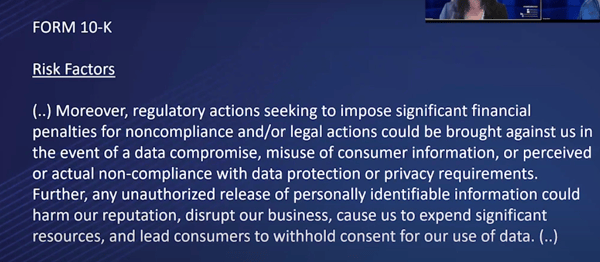
“It’s something you see frequently in risk factors, ‘could’ or ‘may’ or ‘might’… If you know you have a breach or other security incident that is covered by this disclosure, and you’re talking about it as a hypothetical…this isn’t going to work.
“We brought two significant cases in this area…Yahoo had a data breach and hackers stole personal data relating to 500 million of the company’s user accounts…Yet for two years, their disclosures continued to say something along the lines of ‘we might be subject to this risk of a data breach’ when in fact they had been.
“Facebook...was the same kind of language. You saw ‘may’ being used in disclosures when in fact for two years, they knew they had user data that was being mis-used….
“The other thing I would say, don’t think any kind of one-size-fits-all disclosure is appropriate. Any time you are calibrating your risk exposure, you should be thinking about your particular company.”
What about companies that may not have the best possible cybersecurity posture. Is there a potential you could go after those companies as well?
“Thus far, we have only brought cases where there were egregious circumstances, an incident wasn’t disclosed…
“But I could envision a situation where an issuer has some deficiency or a vulnerability that hasn’t necessarily been exploited that becomes public for some reason...If they come out and start doing damage control and they make statements that are not fulsome, are not accurate, that overstate their response, then you may have a problem.”
Learn more - Watch the full video of the 2020 FAIR Conference session “Clarifying the SEC’s Expectations for Cyber Risk Disclosures” (FAIR Institute membership required).









