At FAIRCON21, Jack Jones Introduces the FAIR Controls Analytics Model (FAIR-CAM™), the Standard for Measuring the Effectiveness of Cybersecurity Controls
 Jack Jones, creator of Factor Analysis of Information Risk (FAIR™), the standard for quantitative analysis of cyber risk, introduced a new model, the FAIR Controls Analytics Model (FAIR-CAM™), for quantitative measurement of controls efficacy for risk reduction.
Jack Jones, creator of Factor Analysis of Information Risk (FAIR™), the standard for quantitative analysis of cyber risk, introduced a new model, the FAIR Controls Analytics Model (FAIR-CAM™), for quantitative measurement of controls efficacy for risk reduction.
Jack also challenged his audience at the 2021 FAIR Conference to move beyond the cybersecurity profession’s pure focus on controls frameworks and take a systems view of cyber defenses.
FAIR-CAM Resources
FAIR Institute Membership required and sign-in to the LINK discussion board. Join now!
View the FAIR-CAM information page
Download a white paper with a detailed description of the controls analytics model
Watch the video of Jack’s presentation of FAIR-CAM™ to the 2021 FAIR Conference
“If we want to effectively manage a problem space like cybersecurity, we have to account for its complex nature,” Jack said. He drew the analogy to medicine: NIST CSF and similar frameworks are like anatomy, a list of body parts vs. physiology, an understanding of how the parts work singly and together to create body functions.
The security profession has left the “physiology” to subjective judgments, instead of empirical analysis, he argued, a “really a strong contributor to the challenges we face…and why we lose some of the battles we lose to the bad guys.”
Jack challenged the audience to answer three questions:
- What’s the most valuable control in your cybersecurity program?
- What’s the least valuable control?
- Would your answers be the same as someone else’s in the organization?
“As a profession that spends most of its time, money and effort dealing with controls, the fact that we can’t confidently answer these questions – to me that is a huge red flag,” Jack said.
Introduction to the FAIR-CAM™ ModelThe value of any cybersecurity control is in its effect on frequency of occurrence or magnitude of impact of loss events, Jack explained. That can be quantified with the FAIR-CAM™ model in units of measurement (for instance, frequency, probability, or time).
The FAIR-CAM™ model also groups controls by type--Loss Event Controls, Variance Controls and Decision Support Controls--that account for both direct and indirect effects on risk reduction – and sets controls in relation to each other, showing their mutual dependencies as they fulfill their functions.
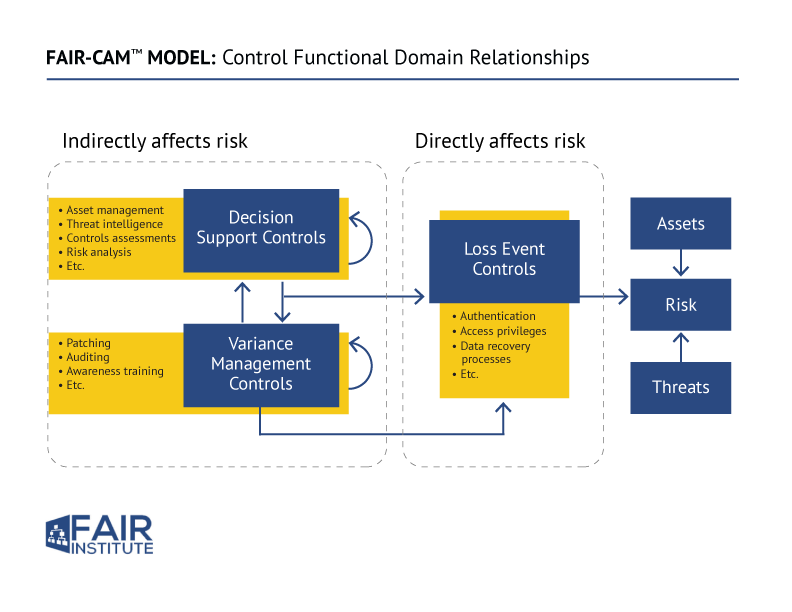
 The model enables a flow-chart view of loss events and controls and empowers root-cause analysis: Jack gave the example of the failure of a (human) control who clicks on a phishing email – that could be traced back to faulty awareness training (a Variance Control) or inadequate threat intelligence (a Decision Control) that didn’t fully inform awareness training on the latest threats.
The model enables a flow-chart view of loss events and controls and empowers root-cause analysis: Jack gave the example of the failure of a (human) control who clicks on a phishing email – that could be traced back to faulty awareness training (a Variance Control) or inadequate threat intelligence (a Decision Control) that didn’t fully inform awareness training on the latest threats.“There are feedback loops and connections here that are not accounted for in any sort of formal, rigorous or reliable way in our profession today,” Jack said. “Now, we can begin to understand where controls fit into the loss event chain…and we can apply the conditions of those controls more effectively in our analysis.”
The FAIR-CAM™ model will be covered under a Creative Commons license similar to how the Open Group and CIS protect their standards. Training programs and a software application are in the works, Jack said.
The FAIR-CAM™ Model Will Change How Cybersecurity Programs Are Managed
Jack discussed some fundamental ways that the new controls analytics model will change industry practice.
KPIs and KRIs for Security Programs
KPIs and KRIs now are “best shots at what metrics should be used and where the thresholds should be drawn,” Jack said. “Under the FAIR-CAM™ model, you shouldn’t have to guess at that anymore. You should be able to identify which controls are most important…This will significantly change how we approach KPIs and KRIs.”
Telemetry
Jack said that the telemetry we have “isn’t always the telemetry we need” and often isn’t in a form that can be effectively used. The FAIR-CAM™ model “will make a huge difference in the way we apply telemetry.”
Frameworks and Maturity Rating
“This should be a really great source of insight into how the controls frameworks we use today could be better,” Jack said. “It will change how we evaluate program maturity.” Working groups of the FAIR Institute are in the process of mapping the new model to ISO 27000, CIS Controls v8, NIST 800-53 and HITRUST and expect to map to MITRE ATT&CK, COBIT, PCI-DSS, and others.
“The FAIR-CAM™ model provides a ‘controls physiology’ view which complements existing frameworks and fills a critical gap in our ability to manage risk effectively,” Jack concluded.









