
 SMEs (that’s subject matter experts) own the systems, the applications, the processes and the business units in your organization—and own the data and insights you need to feed your cyber risk analytics.
SMEs (that’s subject matter experts) own the systems, the applications, the processes and the business units in your organization—and own the data and insights you need to feed your cyber risk analytics.
They are also busy people with limited bandwidth to answer your questions, let alone get their heads out of their work and into yours. So a successful analyst in FAIR (Factor Analysis of Information Risk, the model that powers the RiskLens platform) needs to be an investigator, translator, educator and schmoozer.
Here are three tips from experienced FAIR practitioners on romancing the SMEs to get the data you need.
1. Carefully scope your analysis.
A FAIR analysis starts with a rigorously defined scenario with a clear sense of purpose, namely, to support a business decision, such as “Analyze the amount of risk associated with cybercriminals breaching personally identifiable information (PII) from a ‘crown jewel’ database.”
As in the scenario above, there should be a clearly defined threat (cyber criminals), asset (the database), and effect (loss of confidential data).
Defining the threat, asset and effect points you to the SMEs who keep watch over each of those three elements, for instance your first line of defense against cyber criminals, the business unit controlling an application that might be attacked or your legal team tracking the cost of identity theft services for angry customers. A clearly defined scenario statement also explains to the SMEs what is your purpose for reaching out to them and sets them thinking on the right track.
2. Speak their language
Gathering data for FAIR analysis is a process of filling in with data the relevant boxes in the FAIR Model (see below), with the ultimate goal of quantifying the potential frequency of cyber events that cause loss and the potential dollar value of the losses, based on what you gather from SMEs.
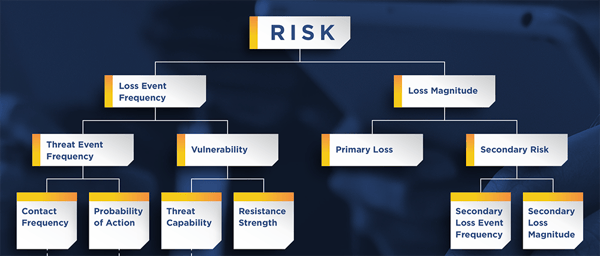
At a recent FAIR Institute breakfast meeting, Robert Immella, the lead FAIR analyst for Key Bank, described how his team learned that structuring interviews with SMEs as exercises in FAIR box-filling was not optimal. So they turned the focus around to the SMEs interests: instead of asking about “vulnerability” (in the FAIR model, the probability that a threat event will become a loss event), they might ask “What’s the likelihood of privileged insiders getting customer data from the XYZ data base?.. Educate them a little bit on FAIR but you still need to speak to them in their language even if it’s technical and with respect to their asset.”
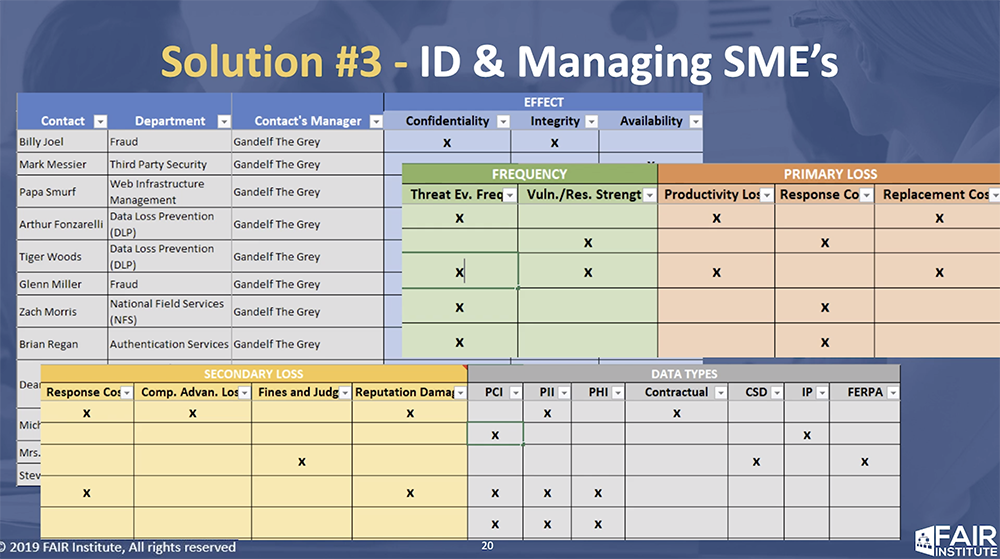
Over time, Robert said, he’s catalogued all the SMEs in his organization by which box in the FAIR model they can fill in, for maximum efficiency in interviewing and data gathering (see his spreadsheet template below).
See the video of Robert Immella's talk to the FAIR breakfast
3. Don’t take “no data” for an answer. Teach calibration.
Most likely, you’ll run into a SME who answers your request for data — for instance on number of potential privileged insider attacks — with “I have no idea.” Jack Jones, creator of the FAIR model, says in his experience, “100% of the time they DO have an idea. Often a pretty good idea. They just don’t know how to approach it.”
The approach is calibrated estimation, starting with a ridiculously wide range and logically narrowing it down to a range the SME has 90% confidence in. (Read Jack’s blog post No Data? No Problem for details.) Remember, the goal of FAIR analysis is to present estimates of risk (or loss exposure) that shows decision-makers a range of probable outcomes. Using ranges brings a higher degree of accuracy to estimates with enough precision to be useful.
Note: If you are working with SMEs who’d like to understand the FAIR model and analysis process, point them to these blog posts:
In a FAIR Risk Analysis, Don't Collect Data till You Scope
To Bring Value in a Risk Analysis, Tell a Story and Provide a Solution
And if they’re interested in the broader case for cyber risk quantification, they can’t do better than reading Jack Jones’ eBook:
An Executive’s Guide to Cyber Risk Economics.
Your best chance to learn FAIR, meet the experts and network with your peers: attend the FAIR Conference (FAIRCON19), Gaylord National Resort & Convention Center, National Harbor, MD, September 24 & 25, 2019.









