 I’ve heard it many times – “Why can’t we just do this analysis over the whole IT environment? Why do we need to pick a specific asset or population or assets?” This may come as a surprise to you or this may be something that has crossed your mind – either way no judgement from me. I am only here to help you understand why it is important and necessary to have the asset(s) defined before performing cyber risk analyses.
I’ve heard it many times – “Why can’t we just do this analysis over the whole IT environment? Why do we need to pick a specific asset or population or assets?” This may come as a surprise to you or this may be something that has crossed your mind – either way no judgement from me. I am only here to help you understand why it is important and necessary to have the asset(s) defined before performing cyber risk analyses.
I get it – choosing just one asset or a population of assets can seem impossible, daunting, and maybe just downright wrong – but it is truly the best way to perform any and every analysis. Let’s think through the issues around properly defining an asset for risk analysis.
1. Focus: “What the heck are you even talking about?”
Imagine showing up to a meeting as a risk analyst; you plan to meet with a group of subject matter experts (SMEs) to gather data for your most recent risk analysis the CISO has asked you to perform. If you show up and ask for data but you cannot tell the SME what you are talking about, they will most likely be very frustrated and maybe even leave your meeting. You’ll end up just talking in circles.
If you go to the same meeting and show up with an asset in mind – say you want to focus on an application that is most likely to be breached, maybe a Claims System – then your audience has something to think about when you’re asking for data.
2. Frequency Counts
Anytime you are scoping an analysis I highly suggest having the FAIR model in front of you, or even better FAIR on a page. Let’s say you are doing an analysis over a breach of PII data. We know most organizations have PII data all over the place, whether it is on a mobile device, a database, an application or just a share drive on your workstation.
The frequency at which an External Malicious Actor would successfully breach a database with PII compared to a mobile device containing PII data is going to be significantly different. Your organization may see lost mobile devices up to once a week with the potential of a device (and its data) getting into the wrong person’s hands. Then think about the times your organization had a database breach -- you may never be able to identify an instance where this happened.
3. Magnitude matters
If we are looking back to the FAIR model, we know that the loss magnitude side represents the amount the organization could lose in dollar terms: How this loss event will materialize. Let’s look at an example of a breach to a database compared to a breach of a user workstation. The workstation may or may not have confidential data on it. If it does have confidential data - say PII - it most likely is pretty limited, for this example let’s say they have 10,000 PII records on their workstation. Then we think about the database that holds PII information as well – this database could hold as much as 5 million records!
If the loss event or breach actually occurs for the application we may see losses in the thousands, but if the organization has a breach of an entire database I can assure you your magnitude will be in the millions. That’s a big difference if you are trying to make a decision based on your overall loss exposure.
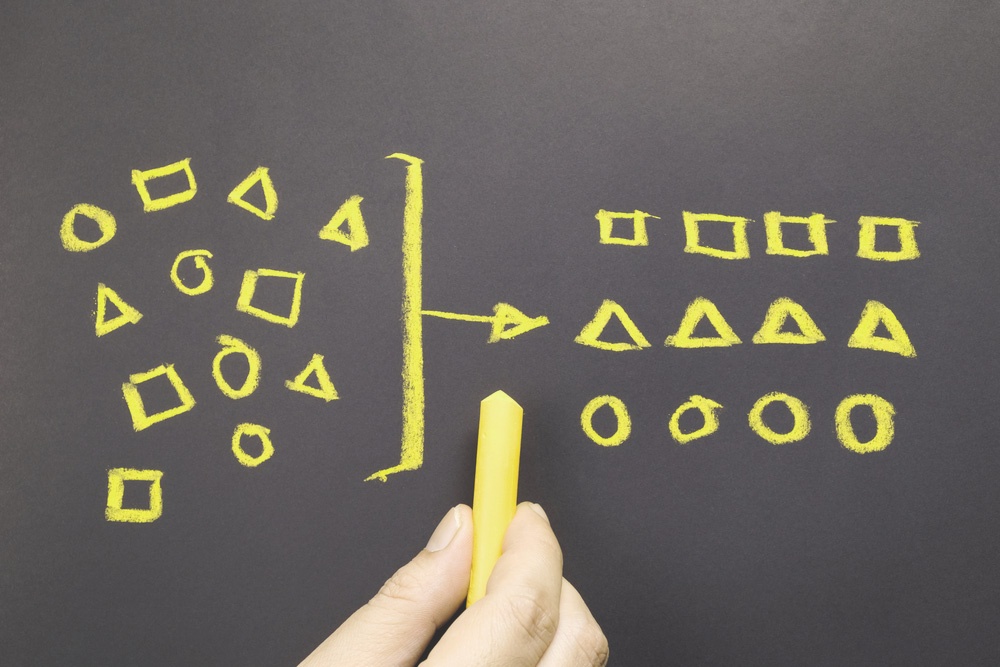
4. Accuracy with a useful level of precision
If you’ve taken the FAIR Training you’ve probably heard this measurement concept before, but I think it is worth mentioning again. When performing a risk analysis we want to focus on being accurate while also providing a useful level of precision. What does this mean? Well, we can’t go to the board and tell them the loss exposure for a certain risk scenario is between $1 and $1 billion. Yes, you are most likely accurate but let’s be honest, that truly does not provide any value. In order to gain some precision, we narrow down the analysis, so we are not talking about the entire IT environment but maybe a population of applications, databases, etc. Finding the focus will help your decision makers to realize the value in your hard work and overall risk analysis.
It may seem tedious at first to break out assets for risk analyses but in the long run it will allow for better and more defensible work. You are working hard to provide value to your organization – just make sure you are seeing the big picture and always focus on the purpose of your analysis. Scoping always matters. To me, it is the most important step in the risk analysis process. If you aren’t sure where to begin start here: How to Scope a Risk Analysis.




.png)




