All-in-One Matrix: Regulatory Compliance Risk Assessment Overview - Updated with NIST CSF + FAIR
Originally published in April, 2019, this summary matrix has now been updated to include the integration of FAIR into the NIST Cybersecurity Framework. NIST has now listed FAIR as an Informative Reference for risk management and risk assessment in the framework. Learn more in this blog post: NIST Maps FAIR to the CSF: Big Step Forward in Acceptance of Cyber Risk Quantification.
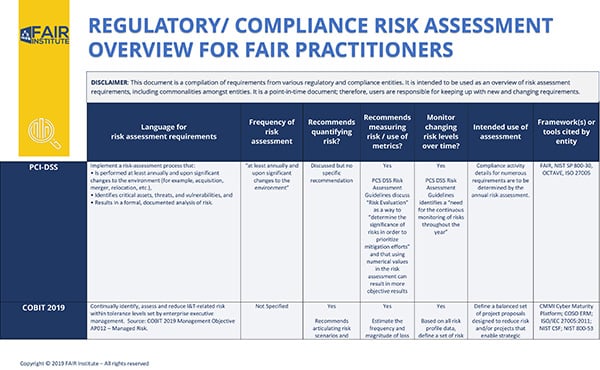
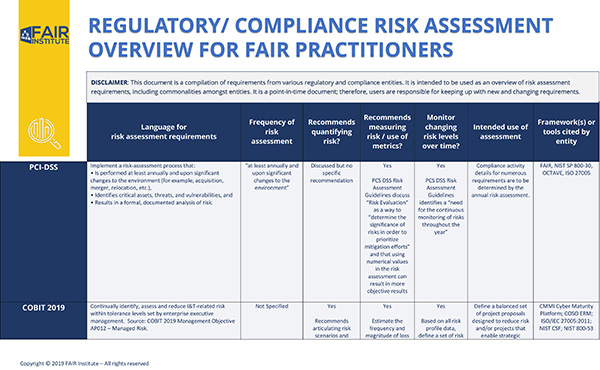
Industry guidelines and standards often strongly recommend or even require a “risk assessment” to satisfy various regulatory and compliance requirements. However, not all assessments are created equal as one entity’s assessment of risk may be another’s control evaluation.
Since risk assessment approaches can range from simple checklists and stratification (red/yellow/green) to weighted scores and probabilistic models, the FAIR Institute Cyber Risk Management Workgroup decided it was high time for some guidance on the topic.
The Workgroup has now published a summary of risk assessment expectations and guidelines from 15 regulatory and compliance entities. This compilation is intended for use by practitioners to explore where the benefits of quantification can be used to achieve stated objectives.
Author Steve Reznik is Director, Operational Risk Management at ADP
The Workgroup analyzed guidance from the 15 leading entities against the following criteria:
- Language for risk assessment requirements
- Frequency that the risk assessment should be performed
- Does the entity recommend quantifying risk?
- Does the entity recommend measuring risk/use of metrics?
- Does the entity require monitoring changing risk levels over time?
- Intended use of the risk assessment
- Framework(s) or tools cited by entity
Download the matrix of risk assessment guidelines from FAIR Institute LINK (Institute membership required).
2018 Cyber Risk Management Workgroup Steering Committee Members:
Greg Rothauser, Sr. Information Risk Manager, MassMutual
Allison Seidel, Information Risk Management, PNC
Steve Reznik, Director, Operational Risk Management, ADP
Brandon Young, Managing Director, Cybersecurity Framework & Risk Assessment, Charles Schwab
Rachel Slabotsky, Risk Consultant, RiskLens, Fmr. Risk Assurance Manager, Ernst & Young
The Workgroup found both commonalities and differences and documented these in a matrix with links to the source documentation. It should be noted that this is a point-in-time document; therefore, users are responsible for keeping up with new and changing requirements.
The Workgroup concluded that in some way, shape or form, a quality risk assessment should identify risks, i.e., the “what?”, and seek an understanding of “how?”, “how much?” and “how much less if we decide to make a change to the control environment?” Since FAIR is all about those “how” questions, then whatever your regulation of choice (or no choice!) says, applying FAIR principles will enable your compliance while helping to optimize risk management decisions.
For more advice on risk assessment characterization:
Risk Analysis vs. Risk Assessment: What’s the Difference?
Control Deficiencies Are Not Risks
Entity specific content:
For Better Risk Assessments in SSAE 18 Audits, Try Quantification with FAIR
Pressing for FAIR: Our Comments and Recommendations on NIST CSF 1.1
The SEC's New Cyber Risk Disclosure Guidance: Textbook Case for FAIR
Does NIST CSF 1.1 Endorse Risk Quantification and FAIR?