The National Institute of Standards has released NIST CSF 1.1, the new version of its popular cybersecurity risk framework—it’s filled with strong implications that infosecurity programs should treat risk in cost-effective or economic terms but never quite comes out and states the words “cyber risk quantification.”
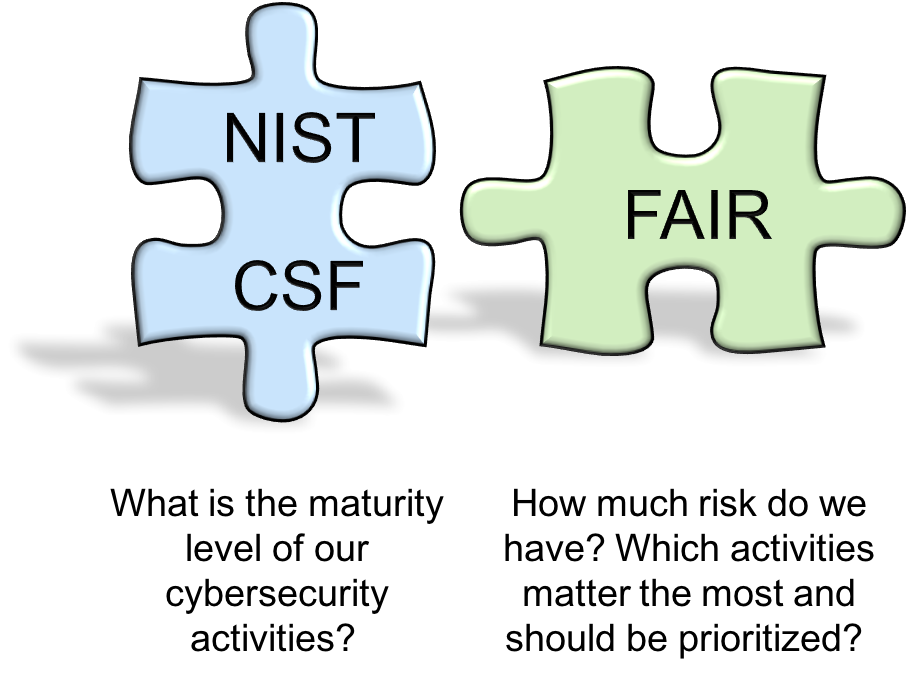
NIST CSF is a very good list of best cybersecurity and risk management practices that organizations can follow as a guide for action as they strive to manage cyber risk. CSF can also be used as a maturity model, where the various activities can be rated using ordinal scales such as 1-5 based on the level of implementation.
While we commend NIST for keeping the list to a reasonable number of recommended activities of just over 100, in practice users still need to prioritize what they should be working on first and decide what level of effort and resources they want to apply to each activity. That's where the mere use of 1-5 ratings won't help you much. After all, does improving an activity's score from 1 to 3 reduce the actual risk more than improving another activity's maturity from a 3 to a 4? How much should one organization spend on improving a given activity based on its score?
Unfortunately, nothing in the NIST document guides users to assess where the biggest probable loss exposures are, to conduct cost-benefit analyses for investments in any CSF activity or to prioritize risk mitigation initiatives based on possible risk reduction, i.e. business impact. All that requires an analytic method to measure cyber risk in financial terms and the effectiveness of these control activities in reducing risk. The CSF never even defines “cyber risk.”
NIST seems to acknowledge this gap, particularly in a new section of the CSF, “Self-Assessing Cybersecurity Risk with the Framework”, where language like this has been added:
“The better an organization is able to measure its risk, costs, and benefits of cybersecurity strategies and steps, the more rational, effective, and valuable its cybersecurity approach and investments will be…
“The development of cybersecurity performance metrics is evolving. Organizations should be thoughtful, creative, and careful about the ways in which they employ measurements to optimize use…
“Verifying achievement of some organizational objectives requires analyzing the data only after that objective was to have been achieved. This type of lagging measure is more absolute. However, it is often more valuable to predict whether a cybersecurity risk may occur, and the impact it might have, using a leading measure.”
Sophisticated risk managers have already found a more “rational, thoughtful and creative” way to use the CSF: combining it with cyber risk quantification. The emergence of standard risk quantification models such as FAIR and recent advances in risk analysis software now allow cyber risk to be quantified in economic terms and managed from a business perspective, without needing to be a statistician or having tons of data available. When analyzed through a financial risk quantification lens, NIST CSF activities can be prioritized and right-sized based on their effectiveness in reducing risk.
There are free tools available for single analyses (FAIR-U or the Open FAIR Risk tool) as well as commercial, enterprise-grade tools such as RiskLens.
Cyber risk quantification is quickly gaining support. Gartner, the influential research firm, now lists risk quantification and analysis as one of the critical components of any effective Integrated Risk Management strategy. Guidance from the US Securities and Exchange Commission points public companies toward disclosure of likely risks in financial terms. Industry leaders and sophisticated cybersecurity shops (like McAfee) are basing their risk analytics programs on FAIR.
And, though NIST does not make any reference to risk quantification or FAIR in the CSF 1.1, NIST did formally review, help edit and endorse a series of blog posts on how FAIR complements NIST CSF, authored by FAIR creator Jack Jones. It’s included on the CSF Risk Management Resources Page– take it as a sign of the future.
3,000 risk professionals have joined the FAIR Institute to network and learn about risk quantification. Join the Institute now.




.png)




