 Cambia Health Solutions, a major health-plan administrator, had managed their HIPAA risk assessments the conventional way, bringing in consultants who ran maturity assessments of the controls around protected health information (PHI) data. And was perfectly acceptable to meet the regulatory requirements.
Cambia Health Solutions, a major health-plan administrator, had managed their HIPAA risk assessments the conventional way, bringing in consultants who ran maturity assessments of the controls around protected health information (PHI) data. And was perfectly acceptable to meet the regulatory requirements.
But Reny Mathew, InfoSec Analyst, and Reid Leake, Information Security and Compliance Analyst at Cambia thought they could get a lot more from HIPAA assessments to understand risk in financial terms, provide data for cost-benefit analysis and justify investments for protecting data – with FAIR™ (Factor Analysis of Information Risk).
Watch the 30-minute video of the Cambia session at FAIRCON2020, Enhancing HIPAA Risk Assessment with FAIR. A free FAIR Institute membership is required – join the FAIR Institute now
They saw that nine mandated steps in HIPAA risk analysis…
- Scope the Analysis.
- Identify and Document Potential Threats and Vulnerabilities.
- Determine Frequency of Threat Occurrence
- Determine the Potential Impact of Threat Occurrence
…and so on, all neatly lined up with the FAIR model and method.
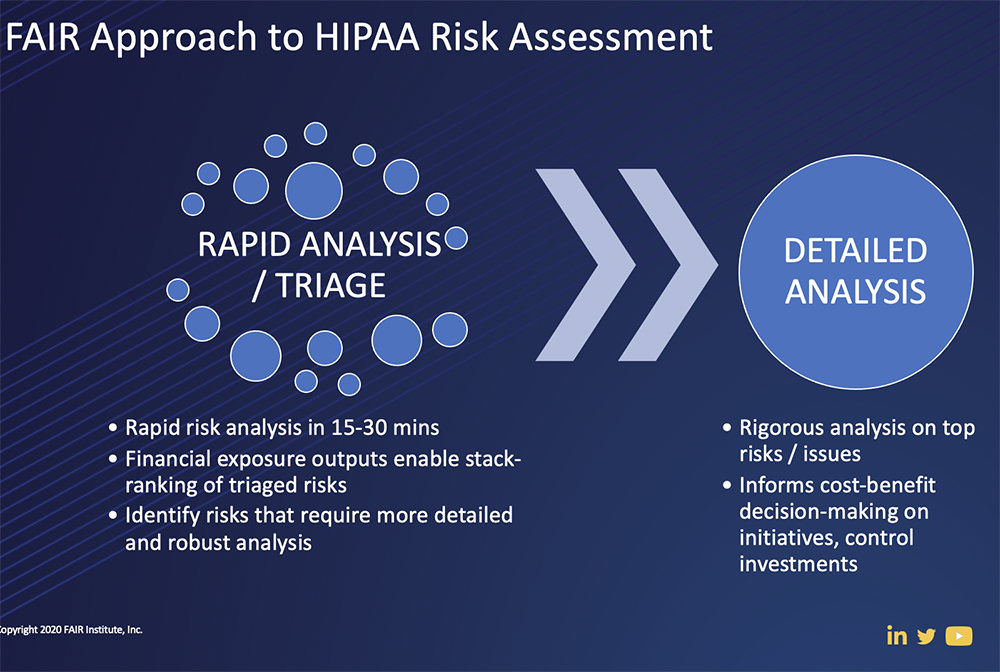
To launch and get up to speed quickly on a FAIR program, Cambia partnered with RiskLens and took advantage of the Rapid Risk Assessment capability of the RiskLens platform. In a three-day period, they identified key assets that were in scope, and a list of 25 primary risks (or loss events), then chose a subset for deeper analysis.
The Cambia team also learned that the collaborative process of gathering data for FAIR analysis—including interviews with SMEs and discussions, even disagreements, among stakeholders -- yields far richer insights than simple controls maturity scoring.
As Reny Mathew explained, the learnings included these points:
- Because of the diversity of participants, the process surfaced a broader range of probable loss events. That helped to “overcome the bias in risk management to high magnitude events—we were able to highlight high frequency events, some of which impacted us daily.”
- Discussions around the notion of a reportable breach made clear that the determination should be based on a more complex set of factors than they had thought: Who accessed the data and how, what the threat actor saw or did, etc.
- “It allowed us to look at our controls in a much more holistic way.” They mapped a threat actor's attack chain to the FAIR ontology and considered the effectiveness of controls at each step. “We could look at controls not as individual components but more so for their effectiveness in working together to prevent loss. It also allowed us to quickly see where we had a concentration of controls within the FAIR ontology and also to understand where we could easily gain the most risk reduction.”
The Cambia team also came away with a list of tips for overcoming challenges in FAIR analysis – watch the video to learn more (but first join the FAIR Institute, free to risk, security and business professionals and students).
Related:
FAIR Institute and HITRUST Plan Integration of FAIR Standard and HITRUST CSF
3 Steps to Combine MITRE ATT&CK and FAIR to Focus Cyber Risk Management




.jpeg)
.png)
.png)


