 One of the questions I like to ask CISO’s is, “What is the most cost-effective control in your arsenal?” The responses are varied and interesting, but their answers are pretty consistently based on bias versus any sort of analytic rigor. If the CISO comes from a hard-core technology background, very often their response will reflect that. If they come from a less technical background, very often that will be evident from their response.
One of the questions I like to ask CISO’s is, “What is the most cost-effective control in your arsenal?” The responses are varied and interesting, but their answers are pretty consistently based on bias versus any sort of analytic rigor. If the CISO comes from a hard-core technology background, very often their response will reflect that. If they come from a less technical background, very often that will be evident from their response.
A more interesting thing happens though, when I ask what their least cost-effective control is. It’s invariably a “deer-in-the-headlights” moment. I have yet to get a confident answer — even a biased one — because as a profession we don’t tend to think in those terms.
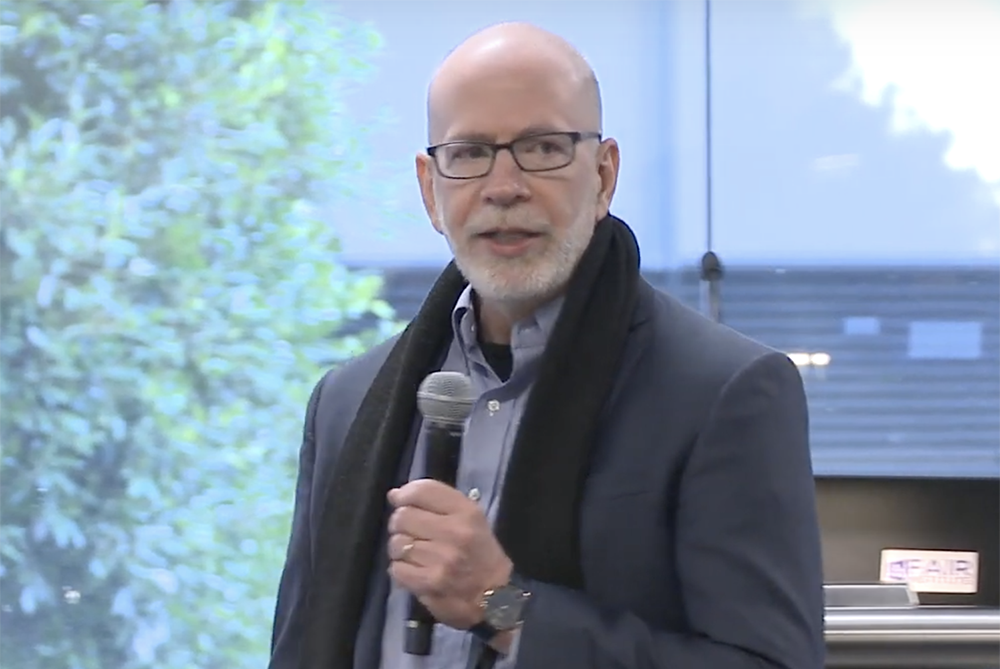
Jack Jones is Chairman of the FAIR Institute, creator of the FAIR model, and author of Measuring and Managing Information Risk: a FAIR Approach.
When business is bad, belts get tightened. And for many businesses, the next few quarters (depending on who you listen to) are going to have a substantial impact on revenue and, therefore, operating budgets. Including the cybersecurity budget. Those new FTE’s for next quarter? Doubtful. Replacements for those FTE’s who leave? We’ll see. That project to implement continuous testing of web applications? Check back with the business stakeholder when this is behind us.
For some CISO’s, it’ll be even more interesting. There will be a knock on their door, and it will be the CFO saying something like, “Plan to shave your 2020 budget by 20% (or whatever).”
As we all know however, the bad actors aren’t on holiday while the rest of us wrestle with COVID-19. So, if we have to make hard decisions about which parts of our programs we focus on and which parts we can scale back on, we’d better start giving some real thought to what matters most. Unfortunately, the kinds of frameworks our profession tends to rely on — those lists of good practices or “control outcomes” — don’t help us much because although they tell us what makes up a cybersecurity program, they don’t tell us which parts matter most. This is where risk-based analyses like FAIR™ can make a difference.
Yes, these types of analyses require more effort than the typical wet finger in the air HIGH/MED/LOW risk rating, but I’m not talking about trying to do deep analysis work here. I’m talking about structured triage — just like in war time — where you save the deep analysis effort for those situations that warrant it.
In risk-based triage, you leverage a well-established model like FAIR and simply populate the variables with the data and/or estimates that you can get relatively easily. The model enforces proper scoping of the measurements, and calibrates how data are applied. Even though lower confidence data introduces a higher degree of uncertainty and imprecision than would be ideal, you still end up with significantly improved results, and without undue overhead.
In times like this, when hard decisions have to be made in a complex and important landscape like cybersecurity, we absolutely have to pragmatically minimize the odds of making poor decisions.
Related:
Watch the Video: Jack Jones FAIRCON19 Keynote “Risk Management Programs that Actually Work”
Jack Jones Honored with SC Media Reboot Leadership Award









