Phil Venables’ 9 Ways to Report Cybersecurity Success – Plus 1 for Risk Quantification
 Cybersecurity wise man Phil Venables – CISO for Google Cloud, Member of the President's Council of Advisors on Science and Technology (PCAST) -- and many more achievements – recently wrote a blog post to help security leaders report on their performance.
Cybersecurity wise man Phil Venables – CISO for Google Cloud, Member of the President's Council of Advisors on Science and Technology (PCAST) -- and many more achievements – recently wrote a blog post to help security leaders report on their performance.
In the post Simple Ways to Communicate Successes, Phil writes:
“All risk programs, but especially security, have the issue that success is often silent, and failure is highly visible. You need to communicate success regularly to provide a wider context for inevitable issues. This might seem self-aggrandizing, but remember, marketing your successes rewards your leadership for their astuteness in supporting your work and thus completes the flywheel of support you need to mitigate future risks.”
Phil then lists nine markers of success, including
>>Incidents, for instance, numbers of phishing emails stopped
>>Vulnerabilities, numbers fixed and the decreasing time to fix them
>>Adjacent benefits, such as launching multi-factor authentication, enhancing the organization’s brand
 And six more, including reporting on cyber incidents at competitors, rationalizing the process for escalating risk management decisions, recruiting other business leaders to praise security operations, highlighting potential incidents that didn’t happen because of careful planning, process improvements, and demonstrating that your team is oversubscribed with service requests from different lines of business.
And six more, including reporting on cyber incidents at competitors, rationalizing the process for escalating risk management decisions, recruiting other business leaders to praise security operations, highlighting potential incidents that didn’t happen because of careful planning, process improvements, and demonstrating that your team is oversubscribed with service requests from different lines of business.
We’d like to respectfully suggest one more way to show success: demonstrate cyber risk reduction by quantifying risk with Factor Analysis of Information Risk (FAIR™). Well, of course we would but Phil himself has spoken highly of FAIR. “I so admire the work that everybody involved in FAIR has been doing over the years,” he said in a session at the 2020 FAIR Conference with Jack Jones, creator of the FAIR standard.
With FAIR analysis, security leaders can speak to the board and senior management in the financial, non-technical terms they understand. By quantifying cyber risk in dollar terms, a CISO can – to cite James Lam, board governance authority speaking at the 2022 Q1 FAIR Conference:
>>Discuss cyber risk in terms of strategic business objectives
>>Relate cyber risk to the organization’s risk appetite, a particular concern of the board
>>Compare risk levels to industry benchmarks
>>Support the board’s legal obligations for risk governance and oversight by providing quantitative proof points to present to regulators
Learn more: James Lam on Critical Do’s and Don’ts of Reporting Cyber Risk to the Board.
How to Quantify Cyber Risk
A cybersecurity leader can identify the organization’s top cyber risks in financial terms by quantifying specific risk scenarios based on their probable frequency and magnitude of impact, for instance:
“Analyze the risk associated with a malicious privileged insider impacting the confidentiality of the PII contained in a crown jewel database by mis-use of their access.”
Learn more: Video: How to Turn Your Risk Register Items into Risk Scenarios You Can Quantify with FAIR
With a top-risks list quantified, a security and risk team can track risk reduction over time and, even more compelling, compare investment in security controls for return on investment in risk reduction. FAIR analysis is always expressed as a range of probable outcomes, giving decision makers a choice of options. As a bonus, quantitative analysis provides a ready answer to demands from auditors to invest in controls based on compliance gaps.
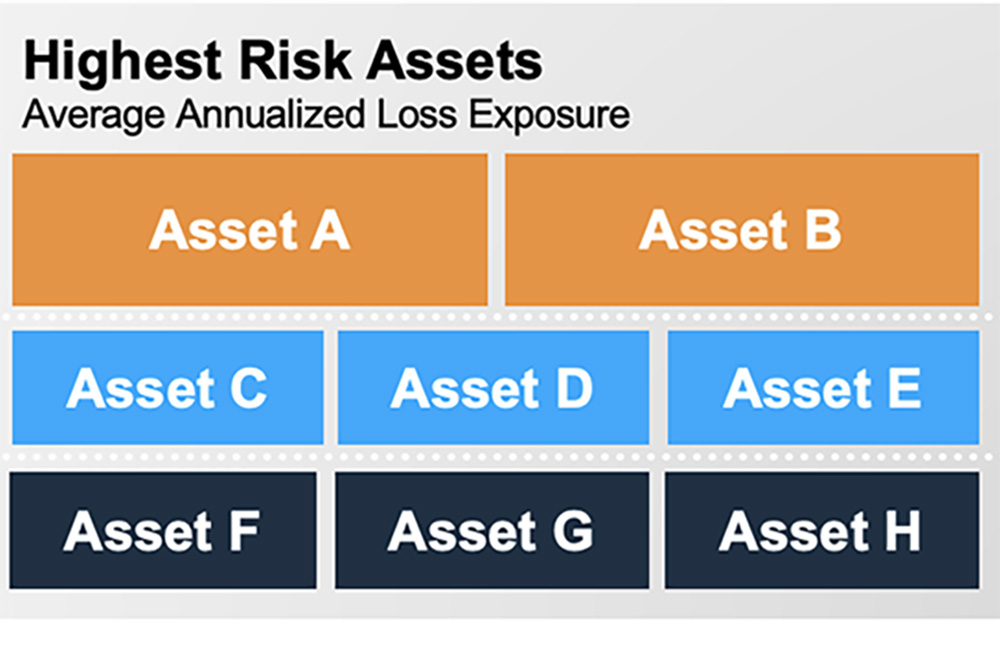
As Phil writes, don’t develop a “merchant of doom” brand by only being known for crisis management. Ongoing quantitative risk measurement gives you the opportunity to control the narrative with regular reporting – and it’s not too “self-aggrandizing” to present to your leadership with a colorful dashboard like this one:
.png?width=1000&height=563&name=RiskLens%20Cyber%20Top%20Risks%20Dashboard%20(3).png)
RiskLens









