Learn How FAIR Can Help You Make Better Business Decisions
Register today
 Here’s a step-by-step look at how an experienced FAIR™ analyst starts with nebulous concerns that may fill your risk register now – items like Privileged Access Management, The Cloud, Data Breach – and shapes them into risk statements to set up a FAIR analysis.
Here’s a step-by-step look at how an experienced FAIR™ analyst starts with nebulous concerns that may fill your risk register now – items like Privileged Access Management, The Cloud, Data Breach – and shapes them into risk statements to set up a FAIR analysis.
It doesn’t take any math at this stage, just putting on your “risk therapist hat,” as Taylor Maze, Sr. Risk Consultant with RiskLens, puts it, to think your way through to defining the specific event you want to analyze for risk.
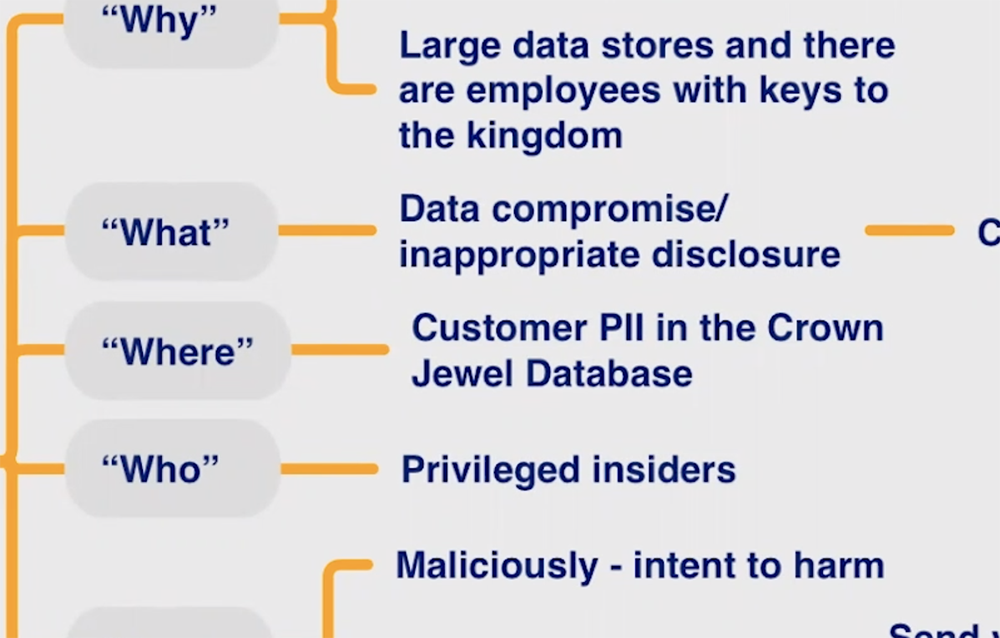
Taylor shows you how she starts with the Why, What, Where, Who and How questions and works to a concise risk scenario with a threat actor impacting an asset resulting in an effect:
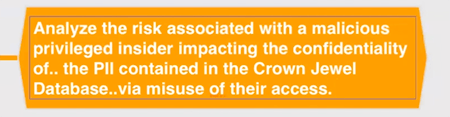
Now an analyst has direction to find the data to fill in the factors for probable frequency and probable magnitude of loss, the two key elements in Factor Analysis of Information Risk – data covering, for instance the strength of the controls in place or the value of the PII.
Get FAIR Training through the FAIR Institute
“All those are possible to think through and analyze in a meaningful way,” Taylor says, “because we’ve gone through the process of fleshing out and documenting what it is that we are concerned about. You are completely set up and prepared to do the quantification” through the application of your choice.
Learn more:
Starting Off on the Right Foot: How to Clearly Define a Risk Scenario Statement for FAIR Analysis
