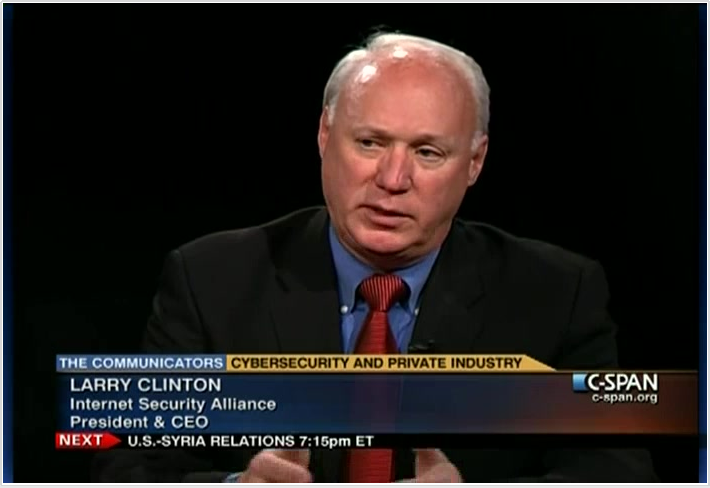
 Larry Clinton has been advocating for cybersecurity in Washington since the days when “I had to start the conversation by spelling ‘cyber’”. President of the Internet Security Alliance since 2003, Clinton has doggedly pushed Congress and successive Administrations to take a holistic approach to information security issues or, as he calls it, the Cybersecurity Social Contract, laid out in a book of the same title, from the ISA.
Larry Clinton has been advocating for cybersecurity in Washington since the days when “I had to start the conversation by spelling ‘cyber’”. President of the Internet Security Alliance since 2003, Clinton has doggedly pushed Congress and successive Administrations to take a holistic approach to information security issues or, as he calls it, the Cybersecurity Social Contract, laid out in a book of the same title, from the ISA.
Hear Larry Clinton speak on the Cybersecurity Social Contract at FAIR Conference 2017 in Dallas, October 16-17.
What’s the story of the Cybersecurity Social Contract?
Ten years ago, or so, there were two prevailing models to address cybersecurity issues.
One was the Bush Administration model, essentially a laissez fair approach with an extremely minimalistic role for the government. The competing model was the Obama Administration’s initial model, a very traditional regulatory model, sort of a Sarbanes-Oxley for cybersecurity.
At ISA, we determined that neither of these models were appropriate—they were 20th century models to deal with a 21st century problem.
We also realized that cybersecurity was more than just a technical problem, it was a three-legged stool. You also needed to deal with the economics that was driving much of the problem, and you needed visionary public policy.
We went back to the way policy makers wisely dealt with emerging technologies in last century, telephony and distributed electricity. Policy makers recognized that we needed universal service, so they developed a social contract.
They said to the companies ‘if you will provide universal service at affordable rates, we will guarantee a rate of return on your investments.’ They made an economic deal and it worked great. The US developed the best telephone system and the best electric system in the world.
We determined that we needed a new partnership between government and business for cybersecurity. We designed a process for government and industry to determine what sort of standards and practices needed to be adopted on a voluntary basis.
We also recognized that there would be a requirement for spending on critical infrastructure beyond the commercial level of security – so you would need incentives.
That’s what became the Cybersecurity Social Contract.
And the Social Contract idea led to the development of the NIST Cybersecurity Framework.
We proposed the development of standards and practices by NIST, and then President Obama called on NIST in an executive order to create that set of standards and practices with industry.
But the executive order said that NIST should create a framework that needed to be flexible, prioritized and cost effective, and it needed to be supplemented with some incentives.
Unfortunately, those elements were not followed. So we’ve had this framework for three years or so and, frankly, we have no empirical evidence that indicates that it has changed any behavior, or improved any security or that the behaviors and the resulting decisions that have been undertaken are cost effective and therefore sustainable.
This is one of the reasons we have been so supportive of the work of the FAIR Institute because it has really taken on the task of developing your own model for using the NIST Framework to assess the cost benefits.
You can’t really deal with this problem unless you deal with the economics.
What are you doing to push the issue along now?
At ISA, we’ve been promoting government action in these areas regularly since the Framework came out and we’ve been seeing gradual adoption of this. The Social Contract model is now the only model being talked about in Congress. It is bipartisan.
We did get information sharing legislation passed. Earlier this year, we saw a bill signed into law that calls on NIST to assess the Cybersecurity Framework for cost effectiveness.
The recently approved—at the committee level—Homeland Security restructuring also calls for this sort of activity with regards to the Cybersecurity Framework.
President Trump recently issued an executive order on cybersecurity. How would you rate the Administration on your issues?
There are elements of President Trump’s executive order that suggest that the Framework needs to be used in government agencies and they need to tie this into their budget process. And there are reports coming out of the agencies that are adopting many elements of the Cybersecurity Social Contract. We are seeing attention paid to economics. They are dealing with this with somewhat greater urgency.
We’re seeing increased funding for cybersecurity. We are seeing some steps being taken to reorganize differently around cybersecurity—the restructuring bill for DHS is one example and there are others pursuant to the executive order.
We are also seeing increased attention from a law enforcement perspective. Law enforcement does a great job but they are vastly underfunded. The first thing is they need more money.
The second thing is they need to reorganize themselves. For instance, the FBI is one of the major investigators of cyber crime but the FBI is still operating essentially like this is physical crime. Treating this like a local matter is something the FBI is now looking at how to restructure.
In Congress and the Administration, we are seeing some increased emphasis across the board on our major recommendations but it’s not happening fast enough. The attacks are getting much more sophisticated. We’re getting not enough help from law enforcement. Nation states are getting more involved even in straight up cyber crime--the North Koreans were behind the Bangladesh bank theft of last year.
So we really need to pick up the pace.
Another focus for the ISA is cybersecurity awareness in corporate boardrooms. What progress are you making there?
It’s really a very encouraging story. In 2014, ISA created for the National Association of Corporate Directors a handbook on cybersecurity that identified five key principles boards need to understand and presented tools they could use to work with their management.
In their global cybersecurity survey in 2016, Price Waterhouse validated that boards of directors were not only using the handbook but it was resulting in dramatically increased levels of investment in cybersecurity, better risk management and a better culture of cybersecurity.
This year, we’re working with the NACD and international partners to develop an EU-based models. Our goal is that since most companies are global companies, we would like to have corporate boards on a global basis all looking at cybersecurity through the same lens.
In surveys of boards over the last few years, cybersecurity has gone from the number 12 issue to the number one issue for corporate boards last year.
So they are becoming more and more aware of the problem. On the other hand, they are being inundated with everybody in the world coming to them with their own magic formulas and secret sauce. Boards are now asking us for a coherent approach and that’s what we’re trying to provide in the handbook and the various tools that come out of it.
Are Boards taking a more economic view of risk, along the lines of FAIR?
Among the principles in the handbook are that cybersecurity is not an IT issue, it’s a management issue. That comports very well with the approach taken by FAIR where by use of the model, you can put an economic value on these issues so that cybersecurity decisions are business-based, not IT-based.
The final principle is that management needs to bring to the board a sophisticated analysis of their cyber risk: What risk needs to be mitigated or eliminated or perhaps transferred with insurance. I’m of the opinion that you can’t make that kind of sophisticated analysis unless you are using tools that combine the kind of empirical models you get out of FAIR.
Related:
Implementing NIST CSF? Read This First
Metrics? What Metrics? Finding the Missing Link to the NIST Cybersecurity Framework









