

Why Third-Party Risk Has Entered the AI Era
Understanding the Generations of Third-Party Risk Management
Cyber Risk Has Moved Beyond Your Perimeter
For CISOs and cyber risk leaders, third-party risk is no longer a governance exercise—it is an operational reality that directly impacts security posture, business resilience, and decision-making.
Authors:
Nick Sanna
President, SAFE Security | Founder, FAIR Institute
Alexander Antukh
CISO, Aboitiz Power | Board Member, FAIR Institute
Today’s enterprise is not just interconnected—it is interdependent. Your environment now includes:
- Vendors with direct access to sensitive data
- Service providers embedded into critical workflows
- Platforms influencing operational continuity
- And increasingly, AI systems interacting with enterprise data and decisions
The rapid adoption of generative AI platforms such as ChatGPT, Claude, and Gemini has fundamentally changed the nature of third-party risk.
These are not static vendors. They are dynamic systems that:
- Continuously learn and evolve
- Process sensitive enterprise data in real time
- Influence decisions, automation, and outputs
- Introduce new categories of risk: data leakage, model behavior, and systemic dependency
As a result, the core question for cyber leaders has shifted:
Not: “Are our vendors compliant?”
But: “Do we have continuous control over the risk introduced by our extended—and increasingly AI-driven—ecosystem?”
Answering that requires rethinking how third-party risk management (TPRM) actually works.
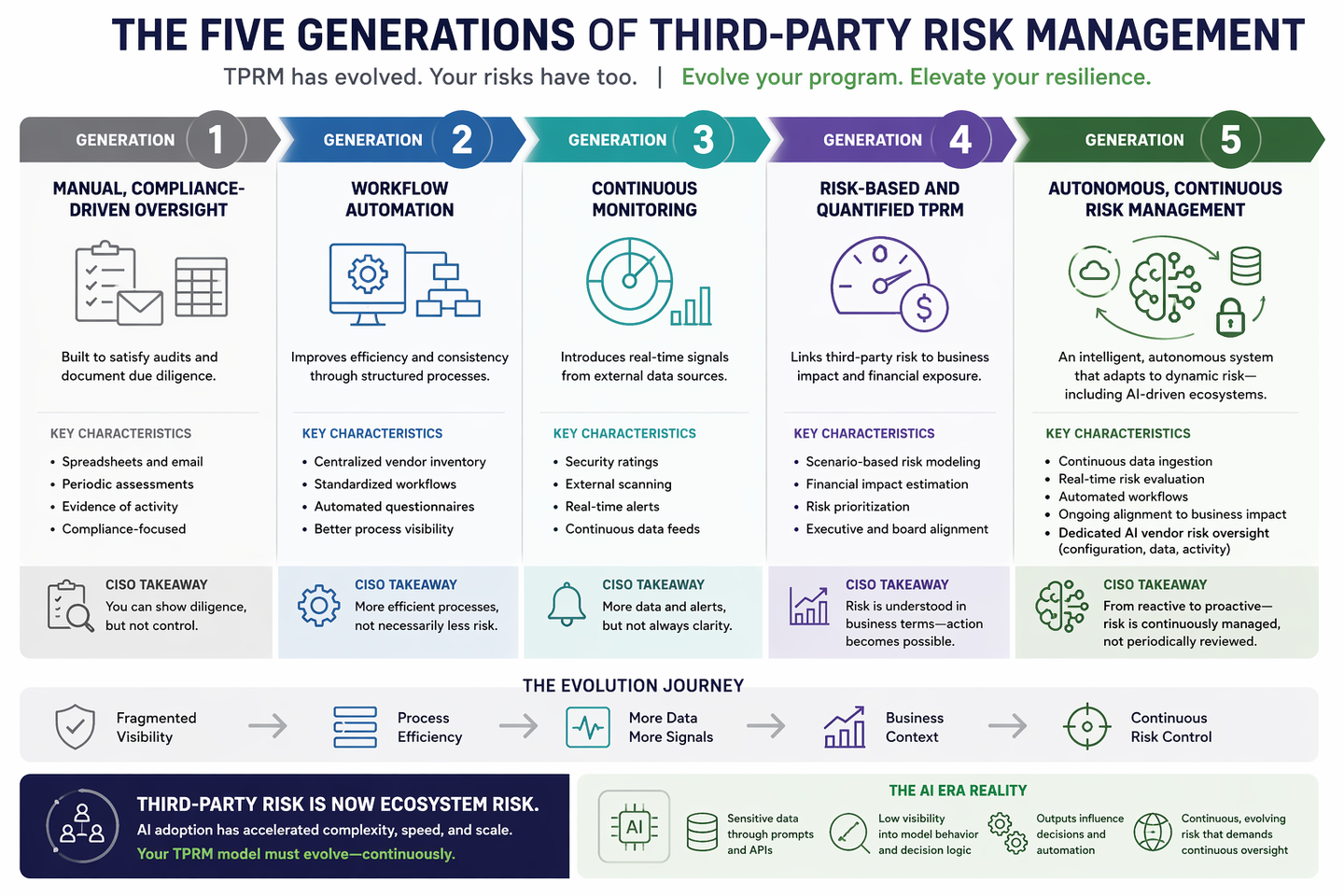
The Five Generations of Third-Party Risk Management
TPRM has evolved through five generations. Most organizations operate across multiple generations simultaneously—creating fragmentation and limiting effectiveness.
Generation 1: Manual, Compliance-Driven Oversight
The starting point for most programs.
Characteristics:
- Spreadsheets and email-based questionnaires
- Periodic vendor reviews
- Audit-driven processes
CISO reality:
You can demonstrate diligence—but not control.
This model answers: “Did we check the box?”
It does not answer: “Are we exposed right now?”
Generation 2: Workflow Automation
To scale operations, organizations moved into GRC-based platforms.
Characteristics:
- Centralized vendor inventories
- Standardized workflows
- Automated questionnaire distribution
CISO reality:
Efficiency improves—but risk understanding does not.
You have better process visibility, but still lack:
- Real-time insight
- Business impact context
- Actionable prioritization
Generation 3: Continuous Monitoring
The shift toward external signals and real-time data.
Characteristics:
- Security ratings
- External scanning and telemetry
- Alert-based monitoring
CISO reality:
You now have more data than ever—but not necessarily better decisions.
You are managing:
- Noise instead of signal
- Alerts instead of outcomes
Key problem: Without linking signals to business impact, you cannot prioritize effectively.
Generation 4: Risk-Based and Quantified TPRM
A major step forward—introducing business context.
Characteristics:
- Scenario-based risk modeling
- Financial impact estimation
- Alignment with enterprise risk frameworks
CISO reality:
For the first time, you can:
- Translate cyber risk into business terms
- Prioritize based on materiality
- Engage executives with credibility
But limitations remain:
- Assessments are still periodic
- Data is often manually aggregated
- AI vendor risk is not fully addressed
Generation 5: Autonomous, Continuous Risk Management
This is where TPRM becomes operationally aligned with how risk actually behaves.
Characteristics:
- Continuous ingestion of internal and third-party data
- Real-time risk evaluation and prioritization
- Automated assessment and remediation workflows
- Persistent alignment to business impact
And critically for the AI era:
- Configuration awareness (How AI systems are set up)
- Data awareness (What data is being shared)
- Activity awareness (Prompts, outputs, logs, usage patterns)
CISO reality:
This is the first model that allows you to:
- Keep pace with dynamic risk
- Scale without linear headcount growth
- Move from reactive to proactive control
- Operationalize risk-based decision-making
Why This Shift Is Now Urgent
For cyber leaders, this evolution is not theoretical—it is driven by four hard realities:
1. Scale Has Broken Traditional Models
You are no longer managing dozens of vendors—but thousands.
And now:
- Every team is adopting AI tools
- Many are unsanctioned or poorly governed
Manual and periodic models simply cannot keep up.
2. Risk Moves Faster Than Your Processes
Risk is no longer episodic. It changes continuously through:
- Vulnerabilities
- Misconfigurations
- Threat activity
- AI model behavior
If your assessments are point-in-time, your understanding is outdated the moment it’s produced.
3. AI Vendor Risk Is a New Class of Exposure
AI introduces risks that traditional TPRM was never designed to handle:
- Sensitive data leakage through prompts and APIs
- Lack of transparency into model decision logic
- Outputs influencing critical business decisions
- Continuous evolution of model behavior
Unlike traditional vendors, AI systems are:
Persistent, adaptive risk surfaces
Which means:
Your risk management must be equally continuous and adaptive.
4. Expectations Have Changed
CISOs are now expected to:
- Quantify cyber risk in business terms
- Demonstrate continuous oversight
- Govern AI-related risks explicitly
- Support faster, defensible decision-making
This is no longer about reporting—it is about operating risk management as a core business function.
Key Questions Cyber Leaders Must Now Answer
To operate effectively in this new environment, CISOs and risk leaders should be able to answer:
Visibility
Do we have a real-time, enterprise-wide view of third-party risk—including AI usage?
Materiality
Can we quantify the business impact of our most critical vendor and AI dependencies?
AI Risk Exposure
Where are AI systems embedded in our workflows—and what risks do they introduce?
Data Governance
What data is being shared with AI vendors—and how is it controlled?
Continuous Control
Are we monitoring configuration, behavior, and usage—not just compliance?
Scalability
Can we scale risk management alongside vendor growth and AI adoption—without scaling cost and complexity?
The Real Shift: From Managing Vendors to Operating Risk
At its core, the evolution of TPRM reflects a deeper transformation in cybersecurity:
- From manual → automated
- From periodic → continuous
- From reactive → proactive
- From process → outcomes
- From vendor-centric → ecosystem-aware
For CISOs, this is not just a tooling shift—it is an operating model shift.
Closing Perspective
Third-party risk is no longer a supporting function. It is a primary driver of enterprise risk exposure.
The rise of AI has accelerated this transformation:
- AI vendors are now embedded in core workflows
- They influence decisions, data flows, and automation
- They introduce new, systemic forms of risk
Traditional TPRM approaches were not built for this reality.
Going forward, the defining capability of leading cyber organizations will be:
The ability to continuously understand, quantify, and manage risk across an extended, AI-driven ecosystem.
The question for CISOs is no longer whether third-party risk is important.
It is:
Are we operating a model that can keep up with how risk actually behaves today?
Interact with your professional peers in redefining cyber risk management. Join us with a FAIR Institute Individual Membership.




.png)



