[Video] FAIRCON18 Table Top Exercise: Pay or Not Pay on Ransomware?

 You’re the CISO of a Fortune 1000 company and the VP of sales comes to you with the typical ransomware lock on a laptop screen. The VP says there’s a $10 million sale that can’t be closed because all the deal data is sitting on the local laptop, not the network. The VP wants the company to pay the 3,000-bitcoin ransom. What’s your recommendation?
You’re the CISO of a Fortune 1000 company and the VP of sales comes to you with the typical ransomware lock on a laptop screen. The VP says there’s a $10 million sale that can’t be closed because all the deal data is sitting on the local laptop, not the network. The VP wants the company to pay the 3,000-bitcoin ransom. What’s your recommendation?
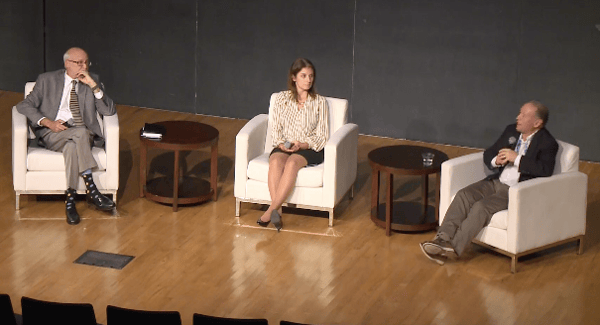
That was the scenario posed by Kim L. Jones (photo right), Director of the Cybersecurity Education Consortium of Arizona State University and FAIR Advisory Board Member, to kick off the panel discussion “Ransomware: Pay the Ransom or Pay More by Dealing with the Consequences?” (requires FAIR Institute membership to view) at the recent 2018 FAIR Conference at Carnegie Mellon University.
Watch the video to see a panel of pros—Alan Levine, former CISO of Alcoa, Summer Fowler, Technical Director, CERT Cybersecurity Risk and Resilience Directorate at Carnegie Mellon’s Software Engineering Institute (SEI), and Chip Block, Vice President at Evolver, Inc. consultancy—think their way through all the angles of a ransomware attack:
- When and how to involve corporate communications, legal counsel, the board or your insurance company.
- What’s a ransomware figure that might be worth paying.
- Damage assessment – is it really just one laptop or is the ransomware itself a planned distraction from a much larger attack?
- Should you report the attack to law enforcement? Make it public?
Just to make it more interesting, Kim keeps ratcheting up the stakes. By the end it’s the CFO’s laptop and the quarterly earnings report is tomorrow, raising the risk of a hit to the stock price if the report is delayed.
Allan Levine staunchly maintains there is no scenario to justifying a ransomware payment:
“You don’t want to become the company that’s known as the cash register…They will keep draining you till you get to the point that it's silly to pay. My advice from the beginning is it’s silly to pay.” Watch the video to see the different takes from Summer and Chip.
One thing the panelists agree on: Planning for ransomware with quantitative cyber risk analytics is necessary exercise. As Summer says:
“This is why I like the proposed ransomware scenario. Your organization has to be able to quantitatively define its risk appetite across a set of criteria, from reputation to revenue to safety, all of these different factors that come together. Our job as the CISO...is to then identify those assets that are most important to achieving the targets and goals that keep us within our risk appetite, and then applying controls around those to say ‘Alright, this is what helps us do that.’”
Chip Block agrees: “If you are FAIR-based company, you would be in a much better spot to make these decisions…You would have put a quantitative number on your assets, including that laptop."
Watch the video of the panel discussion “Ransomware: Pay the Ransom or Pay More by Dealing with the Consequences?” (requires FAIR Institute membership to view).
Related:









