Analyze the Risk of Ransomware – 5-Step Guide for Quantitative Analysis

 In a recent webinar “Ransomware, Colonial Pipeline: A FAIR Perspective” RiskLens expert Cary Wise and Mike Radigan, a cyber risk management executive for a Fortune 100 company and Executive Director at consulting firm Business of Security, presented a detailed plan for a ransomware analysis based on the principles of Factor Analysis of Information Risk (FAIR™).
In a recent webinar “Ransomware, Colonial Pipeline: A FAIR Perspective” RiskLens expert Cary Wise and Mike Radigan, a cyber risk management executive for a Fortune 100 company and Executive Director at consulting firm Business of Security, presented a detailed plan for a ransomware analysis based on the principles of Factor Analysis of Information Risk (FAIR™).
Follow these steps to gather the data for the FAIR factors and run an analysis to learn the probable range of your loss exposure, then determine your most cost-effective opportunities for reduce ransomware risk:
Step 1. Scope the Work
Scoping is the critical first step to bring risk down from the level of fear and uncertainty to analyzable factors. With the help of subject matter experts, FAIR analysts identify the information technology assets in scope and the business processes and operations dependent on them. Read 3 Key Steps to Scoping a Risk Analysis.
Learn FAIR Analysis Fundamentals through the FAIR Institute.
Step 2. Develop Risk Scenarios
FAIR analysis depends on risk scenarios with well-defined threat actors and assets under attack. Sample:
“Analyze the risk associated with a malicious external actor impacting the availability of the PII in a crown jewel database via a foothold gained through phishing.”
SMEs from security operations, threat intel or other teams can help narrow down the scenarios to the most probable for the organization. Video: How to Turn Your Risk Register Items into Risk Scenarios You Can Quantify with FAIR.
Step 3. Collect the Data for the FAIR Factors
With the scenarios defined, analysts can start quantifying the factors that will support the analysis, such as
>>Estimating probable frequency of ransomware attacks
>>Estimating the susceptibility of the controls in place around the assets, as well as the organization’s capability to detect and respond to attack.
>>Loss magnitude estimates – what loss of availability would cost in terms of lost business or other effects
Read more on loss magnitude and loss event frequency.
Step 4. Model the Scenarios
Using an application or spreadsheets and Monte Carlo simulation, and drawing on the estimates for the various factors, FAIR analysts produce a range of probable outcomes in financial terms for loss exposure for each of the scenarios. Learn more: What Is a Cyber Value-at-Risk Model?
((image fair analysis))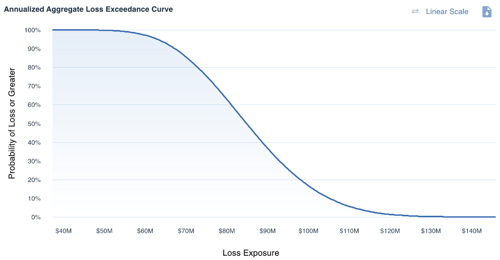
Step 5. What-if Analyses to Support Business Decision-making
By adjusting the FAIR factors, analysts can gauge the effect of implementing or changing controls or business processes to show the way to the most effective ransomware responses – for instance, reducing the PII in a crown jewel database or increasing anti-phishing controls to reduce frequency of attacks. Learn more: How to Model Controls in a FAIR Risk Analysis









