
“ Leadership Vision for 2022,” a new report from Gartner, the leading technology consulting firm, presents some solid advice for CISOs and other security and risk management leaders pulled in many directions by emerging threats, digital transformation and other forces crowding their agendas:
Leadership Vision for 2022,” a new report from Gartner, the leading technology consulting firm, presents some solid advice for CISOs and other security and risk management leaders pulled in many directions by emerging threats, digital transformation and other forces crowding their agendas:
“Prioritize three to five things you own and control that have the greatest impact on business value priorities.”
Understanding cyber risk in terms of business value is the basic deliverable of risk management with Factor Analysis of Information Risk (FAIR™), the international standard for risk quantification in financial terms.
Gartner suggests that CISOs might ‘own’ the following areas in the category of Risk Mitigation – and we’re adding some advice from FAIR practitioners on how to get there.
Operational Downtime
With all the concern about corporate resilience these days, Gartner chose to lead its list with this risk category – and FAIR Institute partner Protiviti has a detailed case study Understanding Changes in Resilience Risks from Technology Advancements that demonstrates a FAIR response. The common measuring standard of recovery time objectives (RTOs) is inadequate, Protiviti argues, because it doesn’t cover service or process-level recovery – and isn’t in step with regulators who are increasingly demanding a quantitative analysis for business interruption. Read the Protiviti case study to learn how to break down loss magnitude for incident response, productivity loss and replacement cost to better quantify operational downtime.
Reputation Loss
Reputation loss is a notoriously hard thing to measure – but is it? In a presentation to the 2019 FAIR Conference, Douglas Hubbard, author of How to Measure Anything in Cybersecurity Risk made the case that this form of loss is wide open to measure with FAIR techniques: “This is one area where you have all the data”. Don’t start with stock price declines; multiple studies have shown that they aren’t a reliable indicator of reputation loss. Instead, estimate loss magnitude with costs of consumer outreach and identity protection, legal liabilities and what Hubbard called “penance projects,” major improvement to security to demonstrate contrition.
Compliance and Audit
Truly a great opportunity for CISOs to step up and own the processes of compliance and audit that have the power to create much busy work detached from economic value. This blog post from a former auditor Reacting to IT Audit Findings? Get Ahead of Them with Cyber Risk Quantification! lays out the hazards of a controls-only focus and recommends using the steps of FAIR analysis to evaluate any perceived controls deficiency: 1) define a loss event scenario, 2) quantify loss exposure, 3) evaluate control improvements on a cost/benefit basis. For more advice, read this post on escaping from qualitative to quantitative risk analysis: How FAIR Helped Me Re-think 3 IT Audit Questions.
Data and Operational Security
Assessing ransomware risk and other hazards for data and operational security is a baseline service of any FAIR cyber risk quantification program. You can see FAIR analysis in action in IBM’s Cost of a Data Breach Report 2021, which demonstrates modeling risk from a ransomware attack on a database containing PII and PCI. IBM concludes that “The FAIR risk quantification methodology can help ascertain the probability of security incidents and calculate the associated costs in business value. Quantifying the cost of a potential breach can help in the decision-making process for allocating resources.”
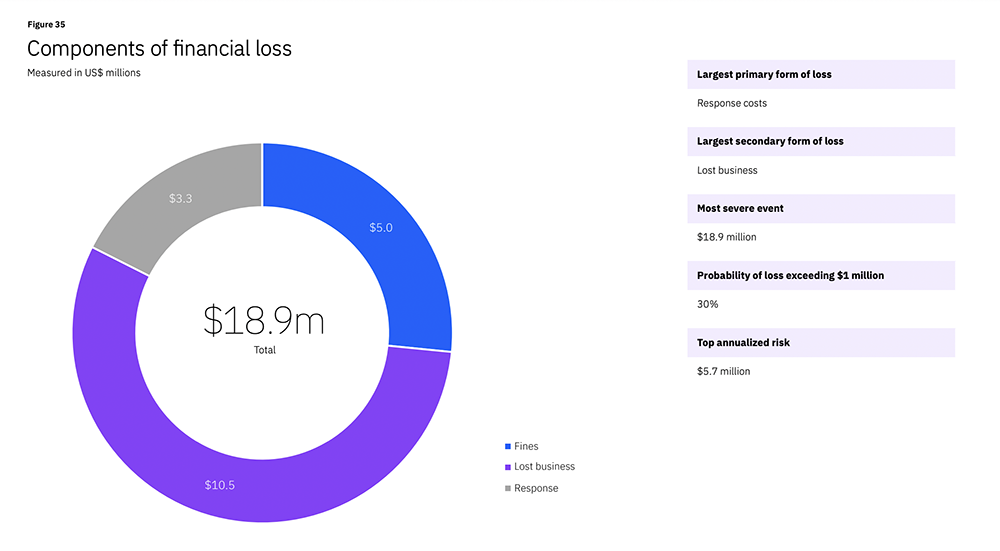 FAIR analysis output from the IBM Cost of a Data Breach Report
FAIR analysis output from the IBM Cost of a Data Breach Report
Vulnerability Remediation
CISA’s Known Exploited Vulnerabilities list today numbers 778, amounting to a mountain of patching that organizations should do, if they have the resources, and they often don’t. In this blog post, How to Turn 10,000 Vulnerabilities into a Manageable Cyber Risk Problem, RiskLens proposes a clever FAIR-inspired solution: shifting focus from a vulnerability-focused approach to an asset-based approach. “This begins by defining “asset profiles,” which are a group of systems that support a critical process; for instance, the four or five systems that are all key to manufacturing. The underlying idea is that if you can understand the business impact at the asset level, you can prioritize vulnerability remediation that way.”
Join the FAIR Institute, receive a free consultation with a FAIR enablement specialist.




.png)




