Q&A: Teaching FAIR to “Security Warriors” at Arizona State University

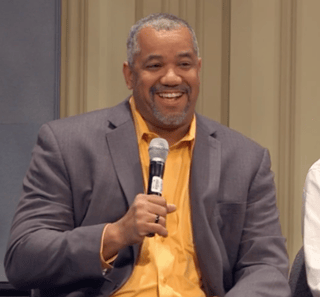 Kim Jones is a 30-year cybersecurity and intelligence veteran – his most recent private sector job was CSO at credit card processor Vantiv, where he started experimenting with FAIR more than five years ago. Recently, he turned cyber-educator as Director of the Cybersecurity Education Consortium at Arizona State University. We talked to Kim at the recent FAIR Conference 2017, where he appeared on the panel “What CISOs Need to Tell the Board”.
Kim Jones is a 30-year cybersecurity and intelligence veteran – his most recent private sector job was CSO at credit card processor Vantiv, where he started experimenting with FAIR more than five years ago. Recently, he turned cyber-educator as Director of the Cybersecurity Education Consortium at Arizona State University. We talked to Kim at the recent FAIR Conference 2017, where he appeared on the panel “What CISOs Need to Tell the Board”.
A: Right now, academia is teaching traditional risk models in terms of T x V x A [Risk = Threat x Vulnerability x Asset], and teaching quantitative vs semi-qualitative vs qualitative, and teaching the standard advantages and disadvantages of those -- and evolving to a quantitative state.
Students are also being taught some of the difficulties in getting to a truly quantitative state. In fact, what I built into the governance program we are teaching at ASU – actually, I had Jack Jones come out and teach that block – is some of the challenges with the traditional quantitative model in security and how FAIR goes a long way to solving those problems.
Q: Is there any resistance to teaching a quantitative approach?
A: Actually, I’m not finding any resistance at all.
There are several approaches to security education in academia:
If you talk to my former peers, they are complaining that there aren’t enough people who are going out from education with cybersecurity knowledge. They are railing at the fact that computer scientists don’t learn cybersecurity. They are railing at the fact that academia by its pedagogical stance hasn’t really embraced cybersecurity until now that we are in crisis mode in terms of the bodies.
And even still there is some concern regarding putting together these cybersecurity degrees--in big air quotes--in terms of: Does this mean you know a tool? Does this mean you know one particular lane? That’s great for the entry level, very technical piece. But has the pendulum swung too far in the other direction?
At ASU, we’ve said that cyber is definitely an inter-disciplinary problem. I wrote a white paper regarding Building Security Warrior 2.0 that talks about the interdisciplinary nature of cyber.
So rather than create a single degree, we have a few concentrations, but we’re looking at a framework to teach these KSAs (Knowledge, Skills, Abilities) within our legal program, within our engineering program, within our applied computing program, so we truly can put a holistic, interdisciplinary viewpoint on cyber. And let’s just make sure we are all talking to one another.
With that attitude there is plenty of place and opportunity to say let’s take a new look at how we’re doing risk within the environment and drop this in here and teach kids how to do it better for us. In fact, ASU has embraced that.
Q: In other disciplines, is the expertise there to inform this kind of program?
A: The expertise is there because if you think about it, other disciplines are already touching upon the problem. So you’ve got the standard computer science and software engineering disciplines, you’ve got the business school that’s got its own information assurance programs, you’ve got our public policy group which is doing emergency management and critical response as part of its degrees, you’ve got the law school that’s actually coming into play, you’ve got our forensic science program that’s doing work in cyber forensics as well, as well as our statistics program that actually does fantastic work in terms of solving problems, on top of the applied computing program which I teach under.
So, plenty of places and more coming, to be honest, as we reach out to put the pieces in. It’s really a lot of fun.
Q: And they’re probably open to this because cybersecurity is such a hot topic.
A: Very much so. I believe our approach is unique to the market and provides true value but what I really like is they’ve embraced the fact that creating a degree that’s narrow or that markets well is not necessarily as good a solution as truly looking at the interdisciplinary nature of the problem and figure out how we capture all of the power behind the largest university in the nation, which we are – we’ve got over 100,000 students.
Q: How is the teachability of FAIR. How do you find students receive it?
A: I’m early into this process. I was in the classroom for my first semester this semester. Conceptually for me, it’s greenfield for the students because they’re learning one way, then we’re bringing another way. The young minds are trying to absorb a little better.
One of the things I am eager to see--I adopted FAIR at Vantiv in 2012 and Jack and RiskLens have radically improved upon the toolset. With the tools there – the concepts are simple and straightforward – and it’s the toolsets that allow you to implement in a meaningful way.
Q: Are you going to be trying the new FAIR training app in your program?
A: Oh, absolutely. Since I wrote the security governance program at ASU, and I’m the one teaching it now, I want to take the two-week risk block that I have, throw it out, and drop FAIR into it.
Plus, our statisticians want to get involved in cyber. If we just use the basic statistics that are out there, and apply that to some of the problems that we’re seeing in cyber, I genuinely think there’s another career path for statisticians out there. The statisticians at ASU sit around the corner from me, so there’s a great opportunity for me to not only drop FAIR into my risk calculus but to drop it into the statistics program as well.
So I think there’s plenty of opportunity for FAIR at ASU.
Related:
Announcing the FAIR University Program
Practice FAIR with Our New Web Training App
Learn about FAIR Training and Certification









