

As a member of the FAIR Enablement Specialist (FES) team at the FAIR Institute, I consult for many individuals and teams as they start on their journeys to better risk management through cyber risk quantification with Factor Analysis of Information Risk (FAIR™). As a result, I am asked numerous questions about the FAIR standard day to day.
This question comes up frequently: “Is FAIR compatible with my ongoing security programs?”
The short answer is, yes. In fact, FAIR improves upon existing security practices by introducing a common language for risk that facilitates communication between infosec teams and their stakeholders in the business. By quantifying risk in financial terms, FAIR enables conversations about cybersecurity in the business terms that everyone in the organization understands.
Learn quantitative risk analysis - join a FAIR Fundamentals training course, endorsed by the FAIR Institute
Let’s get down to specifics about how FAIR would fit with and enhance three common security domains:
FAIR + Frameworks and Standards
NIST, ISO, CIS, HITRUST – any of the common standards or frameworks you probably use to guide and benchmark your security processes and controls recommend a risk assessment component, and FAIR fits the bill. In fact, the NIST CSF specifically cites FAIR as one of the resources to fulfill the risk management function, and NISTIR 8286, also names FAIR as a standard of choice for integrating cybersecurity with enterprise risk management. A key point: Frameworks point you to recommended controls and processes, but FAIR analysis shows you how to prioritize among them based on return on investment for risk reduction.
Learn more:
NIST Maps FAIR to the CSF - Big Step Forward in Acceptance of Cyber Risk Quantification
FAIR Institute and HITRUST Plan Integration of FAIR Standard and HITRUST CSF
COSO ERM’s Cyber Risk Guidance Recommends FAIR™
How FAIR & ISO 27001 Work Together
3 Steps to Combine MITRE ATT&CK and FAIR to Focus Cyber Risk Management
FAIR + GRC/Risk Register
“Too often, risk registers become a due diligence dumping ground for everything that turns up from audits, self-examinations, policy exceptions, etc.,” FAIR creator Jack Jones writes (What Belongs in a Risk Register?). “Here’s the catch: None of those things are risks.” One of the main benefits of implementing FAIR is turning a GRC or risk register into a listing of loss events with clearly defined threats, assets and impacts in financial terms that the organization can use to prioritize risk mitigation.
Learn more:
How to Create a Forward-Looking Risk Register by Tony Martin-Vegue of Netflix
Video: How to Turn Your Risk Register Items into Risk Scenarios You Can Quantify with FAIR
Video: How ServiceNow Integrates FAIR into Its GRC (RiskLens)
Gartner Endorses Risk Quantification as Critical to Integrated Risk Management
FAIR + Reporting Cyber Risk to the Business
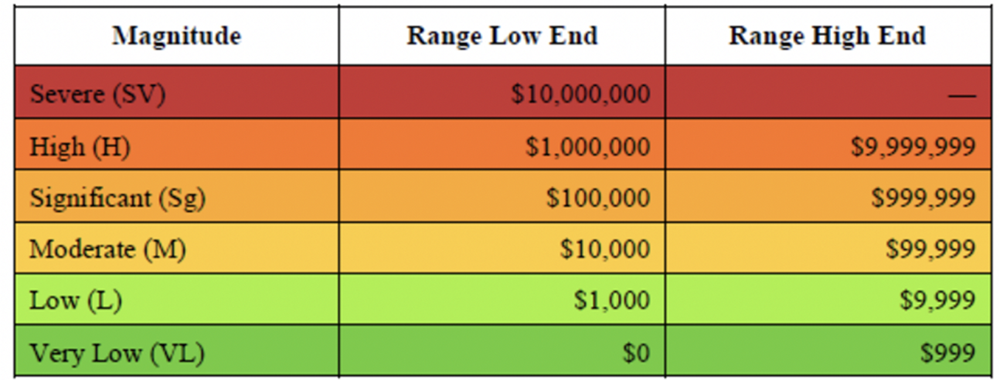
Here’s a concern I hear all the time: “I report to senior management and the board with a heat map based on our team’s qualitative ranking of risks. It’s what they’re used to, not quantitative reporting.” Now, here’s my advice: Stick with your heat maps for presentations but build them based on quantitative analysis. This chart from the Open FAIR Standard is an example of matching colors to ranges of probable loss exposure, as generated by a FAIR risk assessment.
From there, you can start introducing quantification directly into your reporting. And by the way, your board and senior leadership already receive quantitative reports from the non-cyber risk managers, so the transition may be easier than you think.
Learn more:
How to Bridge the Gap Between Qualitative and Quantitative Risk Analysis
4 Steps to a Smarter Risk Heat Map (RiskLens)
NACD Cyber Risk Oversight Handbook Endorses Quantification, Cites FAIR
Define Your Company’s Appetite for Risk with FAIR Analysis
Let's Talk about FAIR
Have questions or would like to set up a time to chat about FAIR? Email the FAIR Enablement Specialist team at fes@fairinsitute.org









