Enterprise Risk Standards – Where does FAIR fit in?


The Operational Risk workgroup meets monthly to discuss uses of FAIR and to share experiences. In August the group tackled the topic of how FAIR fits into the mix of various risk and control standards.
Based on a poll of the group, the most commonly referenced standards are a mix of enterprise frameworks, analytical models, and control checklists, but none other than FAIR really provide any practical guidance for measuring risk (i.e. quantifying risk). For example, the following table is one example of how you might look at the differences between these commonly used standards:
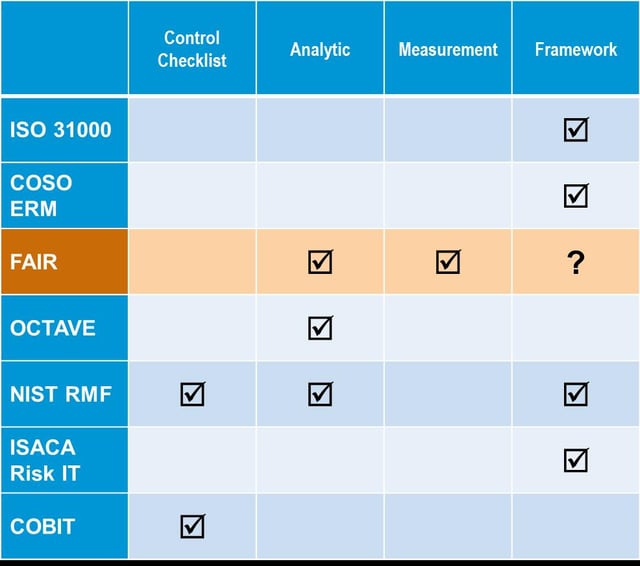
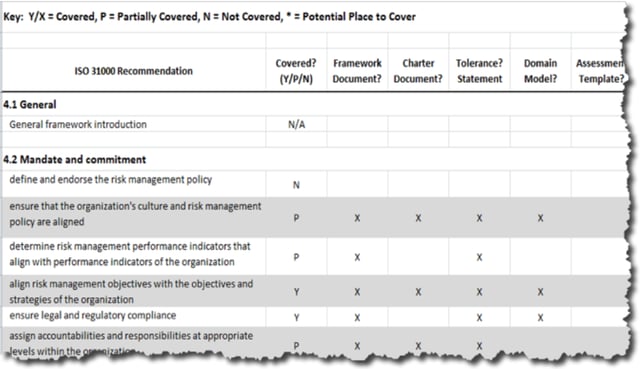
Understanding the differences between what each standard offers and how they might complement each other is essential as risk groups within an organization work together to establish a common vocabulary for risk. Taking a top down approach, you might start with a risk framework such as ISO 31000 or COSO to provide the necessary program level components and activities. For example, ISO 31000 will tell you that you need a risk policy, governance committees, well defined roles and responsibilities, a training program, etc., but it doesn’t help you scope or structure a risk assessment and provides no guidance for measuring risk. The frameworks play an important role by helping you to establish the essential program building blocks and activities. Take any of the available frameworks, and you should be able to map the requirements to your program like this example from one of the workgroup members:
From a bottom up perspective, there are numerous control lists available, such as COBIT and NIST CSF, as well as regulatory and industry specific control requirements such as HIPAA and the PCI DSS. These are at the heart of your compliance program, but they can’t answer some very basic questions:
- What is the cost of choosing not to implement a control?
- Is there an alternative control option that adequately mitigates the risk?
- Is this the most cost effective solution for the same level of risk reduction?
- Is the control achieving the desired effectiveness?
How can an organization really prioritize opportunities to enhance their control environment if they don’t have a methodology to determine how much risk is really reduced? “A lot” or “a little” just aren’t good enough answers in today’s environment. Many of the workgroup members mentioned the desire to understand the economics of risk as a driving force towards adopting FAIR. Whereas a standard like NIST CSF evaluates the control environment using a relative maturity rating (or capability rating), FAIR measures risk exposure using a Value at Risk (VaR) methodology. Essentially FAIR helps you understand how often loss is likely to occur and how bad it’s likely to be. For more information on how FAIR complements control standards like NIST CSF, see this series of blog posts by Jack Jones.
Let’s say your organization has an enterprise framework, and you’ve determined the most appropriate list of controls for your industry, now what? How do you scope a risk assessment, how do you estimate and express the risk exposure, and how do you normalize the results across many types of risk? This is where FAIR fits it. FAIR starts with a single definition of risk that can be used across the enterprise regardless of your function. It provides both an analytical model through the ontology, and also several methods of quantifying risk using a Value at Risk (VaR) model.
One workgroup member described how they use FAIR in conjunction with the Kill Chain concept to communicate cyber risk. FAIR provides the structure for the analysis, but when they want to present the results to senior management, they haven chosen to describe the exposure by mapping to phases of the Kill Chain. This provides a logical and visual representation from a defender’s perspective that is often lacking when cyber risks are discussed.
There are so many possible use cases for FAIR, so many different ways to wrap process around it, and so many examples of how to best communicate the results of a FAIR analysis. In the Operational Risk workgroup, practitioners are sharing tips and techniques so they can get the most out of FAIR. Our next virtual meeting will be on September 27, 2016 at 3:00 PM EDT, and we will be discussing Using FAIR for Low Frequency / High Impact Events. We plan to roll up the sleeves and walk through a use case to demonstrate how FAIR applies beyond the theory.









