Factor Analysis of Information Risk (FAIR™) defines “risk” in a way that’s both simple and useful.
Risk = the probable frequency and probable magnitude of future loss
The factors that make up risk are also easy to grasp in this image of the model – frequency factors to the left, magnitude factors on the right.
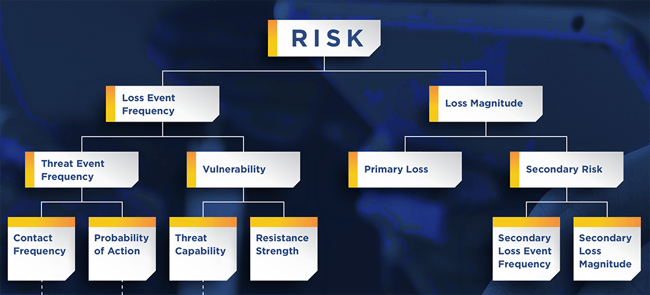
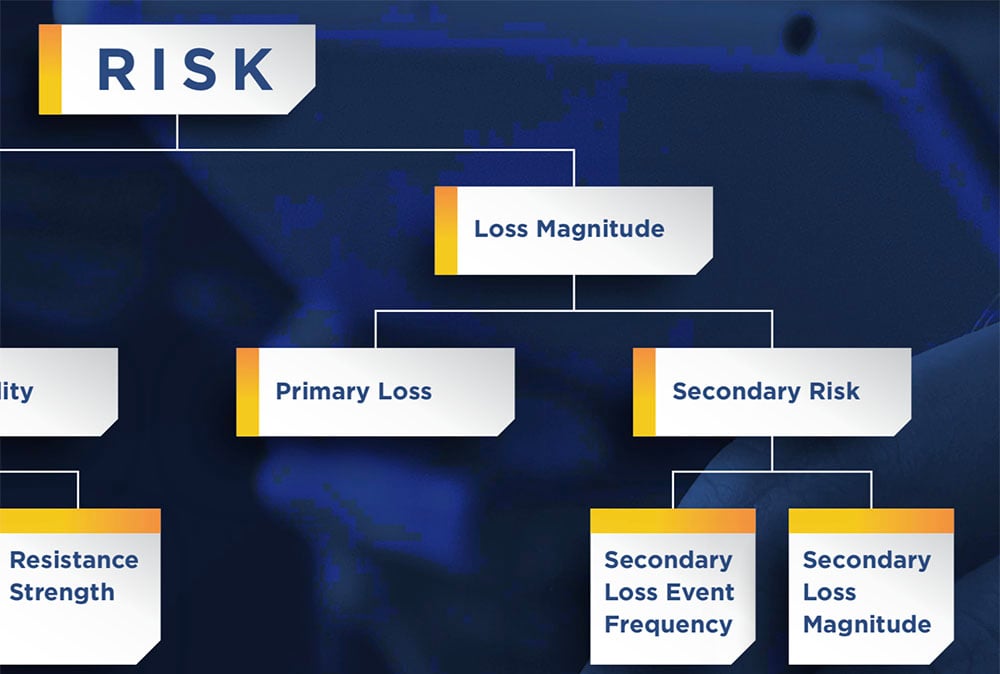
The Loss Magnitude side guides us to put a dollar value on risk, helping to give FAIR its power for business decision support. But wrapped into the definition of Loss Magnitude is a critical first cut at the analysis – whose loss is it? The primary stakeholder – for instance the organization holding the data at risk? Or the secondary stakeholders outside the organization – for instance, the subjects of the data?
Loss Magnitude = the probable magnitude of primary and secondary loss resulting from an event
Primary Loss Magnitude refers to losses incurred from the loss event itself, the results of the threat actor successfully impacting the asset. This also includes activities that the primary stakeholder chooses to do in the wake of the loss event, such as investigating the incident or replacing a damaged server.
Secondary Risk (or Secondary Loss Magnitude) refers to losses incurred from the reactions of outside parties (or “secondary stakeholders”) to the loss event.
Read more: Primary vs. Secondary Loss in FAIR™ Analysis: What's the Difference and Why It Matters
Examples of secondary stakeholders: employees (for instance, if their personal information were exposed in a data breach), customers (ditto for personal information) and regulators with the power to levy fines.
As the image of the model shows, Secondary Risk actually requires its own analysis, based on on the two factors below it. How probable is a Secondary Loss Event - expressed as a percentage – and if that occurs, what’s the probable Secondary Loss Magnitude of that event?
For example, if an encrypted data base with PII is breached, the encryption key is compromised and the attacker now has your data in plain text, the probability of a secondary event – say, a lawsuit by customers leading to lawyer costs or settlements – is highly probable and quantifiable. On the other hand, if there’s no compromise of the key, then there’s low probability of a Secondary Loss Event.
Checklist for the Filling in the Loss Magnitude Factors: The Six Forms of Loss
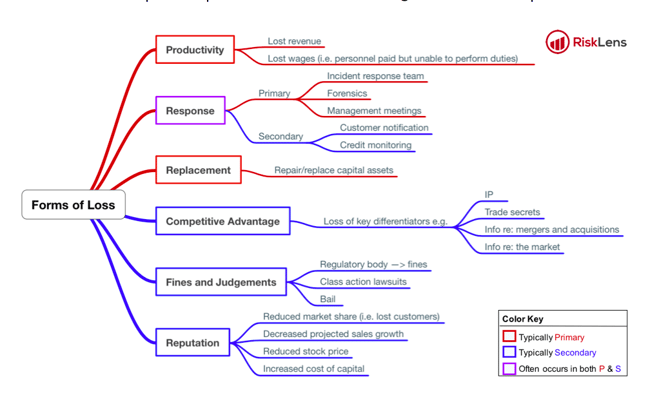
The FAIR methodology also provides a handy way to account for the losses from cyber events, by breaking out six forms of loss:
Productivity: Loss that results from an operational inability to deliver products or services or lost wages on idle workers.
Response: Loss associated with the costs of managing an event
Replacement: Loss that results from an organization having to replace capital assets
Competitive Advantage: Losses resulting from intellectual property or other key competitive differentiators that are compromised or damaged
Fines and Judgements: Costs levied against the organization through civil, criminal, or contractual actions
Reputation: Loss resulting from an external stakeholder perspective that an organization's value has decreased and/or that its liability has increased
How do these six forms of loss shake out into the Primary and Secondary Loss categories? See this mapping, with red for Primary, blue for Secondary and purple for both.
From A Crash Course on Capturing Loss Magnitude with the FAIR Model
Gathering Data for the Loss Magnitude Side of FAIR Risk Analysis
The FAIR Institute blog is loaded with tips about how to collect the loss magnitude data that will drive the output of your FAIR analysis in the financial terms that your organization’s leadership wants to see. Here’s a sampling:
Focusing your data gathering
Finding data inside your organization
- 3 Tips on How to Talk to SMEs about Cyber Risk Quantification
- Secrets to Gathering Good Data for a Risk Analysis
- 3 Ways to Gather Loss Magnitude Data (from Your Cubicle)
Finding industry data
- How to Find Data for Every One of the FAIR Factors – Wade Baker’s Talk at 2020 FAIR Conference (Video)
- Shopping for Cyber Loss Data
Techniques for dealing with sketchy data
Get a complete education in FAIR risk analysis: Take the FAIR Fundamentals training sanctioned by the FAIR Institute.









