
 Good news for organizations interested in adopting quantitative risk analysis but can’t commit much budget or resources: You can begin the FAIR™ cyber risk quantification journey without significant capital investment or a dedicated team. Here’s how:
Good news for organizations interested in adopting quantitative risk analysis but can’t commit much budget or resources: You can begin the FAIR™ cyber risk quantification journey without significant capital investment or a dedicated team. Here’s how:
Use FAIR’s Standardized Terminology for Risk
To build a quantitative foundation, organizations should begin by adopting a common language. Ensure all employees define risk concepts the same way by learning FAIR terminology. Staff can train through the RiskLens Academy or through an informal reading group based on the FAIR book.
Learn about FAIR training and certification
Everyone in your organization likely has different definitions for risk concepts. Many organizations evaluate risk using ordinal scales such as high, medium, low, but how analysts, executives and board members probably define those terms in various ways. Using a common language throughout the organization helps to reduce subjectivity and improves communication by keeping everyone on the same page.
Start Small by Considering the Organization’s History of Cyber Events plus Industry Data
Organizations often don’t think they have the data needed to do FAIR quantitative analysis. Not so. When beginning the quantification journey, organizations should consider the cyber events they have experienced. These could include ransomware or the loss of sensitive data whether by a breach from an external actor or an employee accidentally emailing confidential customer data to the wrong person.
Author Erin Macuga is a Risk Consultant for RiskLens, the technical adviser to the FAIR Institute
Organizations can use those past events to benchmark analysis. Analysts can consider the response efforts to recover from an event, including who was involved and for how long. Other data points would be revenue lost from an outage or number of records exposed and customers lost because of a data breach. Also, the frequency of cyber events and controls in place (or needed) to reduce the risk exposure.
Besides internal data, you can find good data about cyber events and losses by industry in public sources though it can take some hunting around. Get suggestions from these two FAIR Institute blog posts:
How to Find Data for Every One of the FAIR Factors
Analyst should work in ranges to estimate the different factors to capture all potential values. FAIR methodology recommends that ranges should aim for accuracy with a useful degree of precision. Those new to quantitative cyber risk analysis are encouraged to work in wide ranges which is still a far superior approach to the “finger in the air” method. The historical data of an organization and its industry and the use of ranges are a great way to begin quantified analysis of both known risks and cyber events the organization has not yet seen.
 TIP: You can conduct limited FAIR analysis on the free, open-source FAIR-U tool from the FAIR Institute.
TIP: You can conduct limited FAIR analysis on the free, open-source FAIR-U tool from the FAIR Institute.
Fulfill Reporting Requirements from Leadership
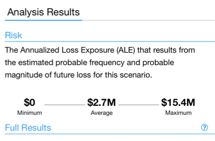
Reporting analysis results to leadership should be done in dollars and cents instead of subjective terminology. The reporting does not need to be beautiful beyond belief but should effectively communicate analysis results based on quantitative metrics that leadership already knows. Furthermore, the analysis and the reports should focus on the risks that matter most to the organization’s mission.
If leadership is most comfortable receiving reporting in ordinal scales, analysts should be able to clearly define in dollars and cents the metrics behind those scales. The risk analyst should discuss with leadership how they would define “medium” in quantitative terms, for instance a range of $500K to $3M, before continuing to present in high/medium/low terms.
Learn more: Qualitative vs. Quantitative Analysis for Cyber Risk: What’s the Difference?
Improve Decision Making
Using a common language and reporting with financial, quantitative values will only improve decision making. For example, an organization was looking at implementing a certain control but were not clear if it was a good investment. Upon completion of the analysis, the leadership of the organization was immediately able to see that the implementation of the control could be justified for return on investment. Organizations can gain an enhanced understanding of the risk exposure they would face from a cyber or operational event and the risk reduction from investment in a control and can be better prepared to budget, respond, and mitigate the event once it happens and prevent it from occurring again.









